What exactly is a vulnerability?
A security vulnerability (also known as a security hole) is a security flaw detected in a product that may leave it open to hackers and malware. Using such vulnerabilities, attackers can exploit the affected system/product for their profit in various ways.
What is an exploit?
Exploits are attacks performed on a system by taking advantage of a particular vulnerability the system might have. They are a sequence of commands which help malware gain privileged access and thereby take control of the infected system.
For instance, the infamous exploit called EternalBlue took advantage of a security vulnerability in Microsoft’s implementation of the Server Message Block (SMB) protocol and launched the biggest ransomware attack in history called WannaCry.
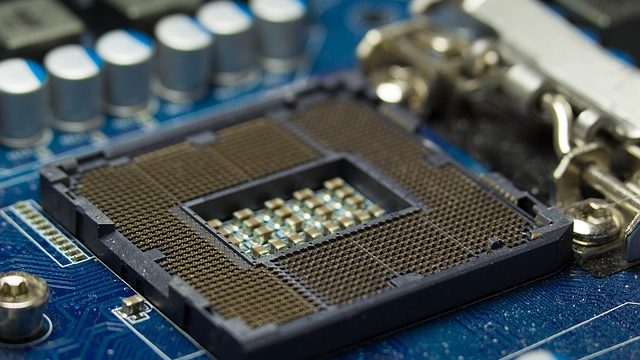
What are Meltdown and Spectre?
- Recently, researchers had found two major vulnerabilities in Intel processors which were introduced after 1995. These vulnerabilities are known as Meltdown (CVE-2017-5754) and Spectre (CVE-2017-5753 and CVE-2017-5715).
- Meltdown and Spectre allow access to recently processed data on the system. Although Intel says that this data cannot be corrupted or erased from the system, attackers can still steal the secure data which does compromise the user’s security.
- Both the vulnerabilities can be used by attackers to spy and steal secure data such as passwords and encryption keys which are present in the cache memory.
- When these vulnerabilities were first discovered, Intel considered them as a small bug. However, later, researchers from Project Zero at Google revealed how severe these vulnerabilities can be.
What does Meltdown (CVE-2017-5754) do?
- Meltdown allows low privileged processes to gain access to high privileged kernel processes to steal system memory.
- It uses side channel information available on modern processors.
- As of now, Meltdown is known to affect only Intel processors.
What does Spectre (CVE-2017-5753 and CVE-2017-5715) do?
- Spectre allows access to the memory of one of the running applications by another application.
- In order to optimize performance, most processors use a technique called ‘Speculative Execution’ where the processor tries to compute the next step or instruction to be executed in advance. If this is not required or if it’s wrong in its prediction, the CPU starts from the beginning of the program. Spectre affect’s processors using Speculative Execution by giving access of one process to the contents of another process running in the memory.
- Spectre vulnerability affects Intel, ARM, and AMD processors.
How do these vulnerabilities affect me?
If your device has Intel, AMD or ARM Cortex-A Processor with Operating Systems such as Microsoft, Linux, Mac or Android, you may experience system performance issues. The severity of the slowdown is, however, still unclear.
What do I do?
- Contact your Operating System vendor or system manufacturer and apply any available security updates as soon as they are available.
- Apply all recommended security patches whenever they are available.
- Keep Automatic Updates ON.
Subject Matter Experts
Alisha Salunke, Shalaka Patil, Suvarna Trigune, Shriram Munde | Quick Heal Security Labs
Content references:
https://newsroom.Intel.com/news/Intel-responds-to-security-research-findings/
https://www.amd.com/en/corporate/speculative-execution
https://developer.arm.com/support/security-update
https://googleprojectzero.blogspot.in/2018/01/reading-privileged-memory-with-side.html
https://security.googleblog.com/2018/01/todays-cpu-vulnerability-what-you-need.html
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/ADV180002