Estimated reading time: 3 minutes
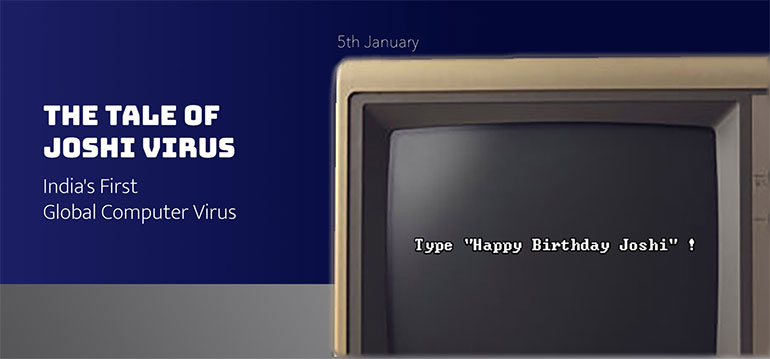
In the cinematic tapestry of cybersecurity, where tales of intrigue and innovation collide, one story emerges from the shadows of the past. It’s a story that began in the early 1990s, during the DOS era, when computer viruses were...
Estimated reading time: 3 minutes
We are observing a rise in fake websites offering investment-related services. Many of these impersonate well-known brands by creating replicas of their official websites. Unsuspecting visitors interact with these fake websites, fall victim to scams, and lose large sums...
Estimated reading time: 2 minutes
The recent data breach at one of India’s largest health insurance companies has left millions of customers vulnerable, raising serious concerns about data privacy and security. With personal and medical information exposed, many are left wondering: How could this...
Estimated reading time: 4 minutes
If you’ve been following the news recently, you’ll undoubtedly have read about cybersecurity incidents impacting corporations of all sizes in all industries around the world. While it doesn’t often make the news, even small- and medium-sized businesses (SMBs) have...