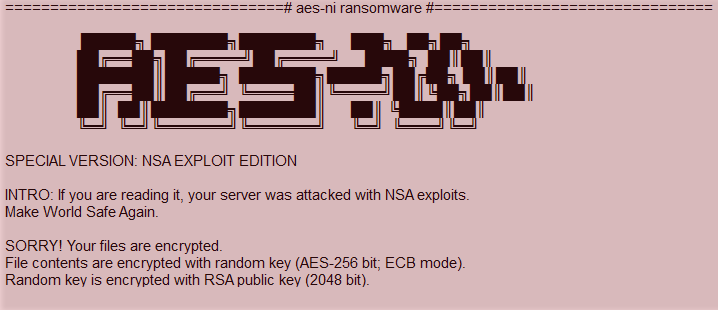
Cybercriminals are adopting unique ways for spreading malware and this has been evident in the cases of the Cerber ransomware where the RIG exploit was used and the WannaCry ransomware which used the SMBv1 vulnerability. And now it’s the AES-NI ransomware which uses a combination of fileless and code injection technique.
This threat involves the abuse of PsExec utility which is a Microsoft Sysinternals command line tool which can execute files on remote systems. The use of PsExec utility highlights that administrative login details have already been known to the attacker somehow.
Similar to Troldesh ransomware, the creators of AES-NI ransomware run brute force attack on Remote Desktop Protocol (RDP) for guessing the login details before transferring the malware to the victim’s computer and infecting it with a ransomware.
AES-NI ransomware harnesses a self-destructive routine after its remote execution which gives it the capability of a fileless malware. This is further enhanced by using code injection in the genuine system process ‘SVCHOST.EXE’ which is responsible for data encryption. The ransomware also enumerates open share folders and connected devices that could be accessed through the network with saved credentials and encrypt the files once access is authenticated.
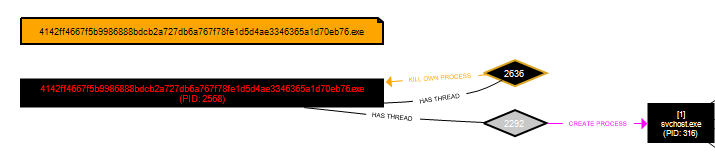
The malware further removes all traces and artifacts such as system’s event logs. It also removes forensic evidence such as prefetch which contains information like files executed on system and timestamps using wevtutil.exe. These activities cannot be traced and thus they make it difficult for security analysts to analyze this malware. The chances of other ransomware adopting similar techniques are extremely high.
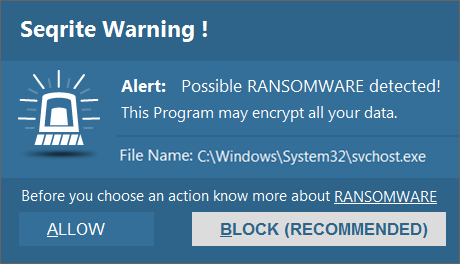
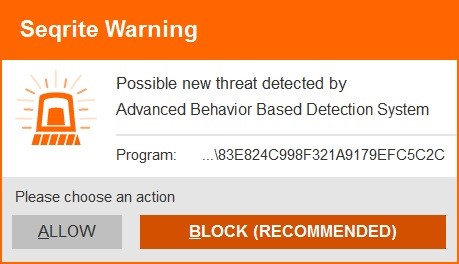
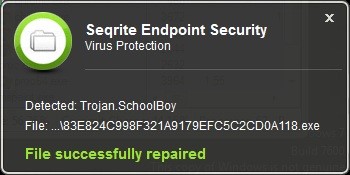
Seqrite successfully detects and prevents the AES-IN ransomware.
Given the extent of the damage a ransomware can do to your data, it is important that you follow the recommended security measures mentioned below.
- Back up your files on a regular basis. A ransomware goes after your files when it infects your computer. If you have a backup of all your important files, there is no reason why you should give in to the ransomware’s demands. Remember to disconnect the Internet while you are backing up on an external hard drive. Unplug the drive before you go online again. Several free and paid Cloud backup services available on the market that can take data backup periodically.
- Provide Read/Write privileges to network shares only when required. Try not to keep open shares as they are likely to fall prey to encryption if there is a ransomware infection.
- Use strong login credentials for both the user and administrator. Weak credentials can be easily brute forced to gain system access.
- Use an antivirus software that gives multilayered protection against infected emails, malicious websites, and stop infections that can spread through USB drives. Keep the software up-to-date.
- Apply recommended security updates for your computer’s Operating System and all other programs such as Adobe, Java, Internet Browsers, etc.
- Do not click on links or download attachments that arrive in emails from unwanted or unexpected sources. Even if such emails seem to be from a known source, it is better to call up the sender and verify them first.
ACKNOWLEDGMENT
Subject Matter Expert
- Shantanu Vichare | Quick Heal Security Labs