Advisory: Middle East Conflict & Cyber Escalation
Overview
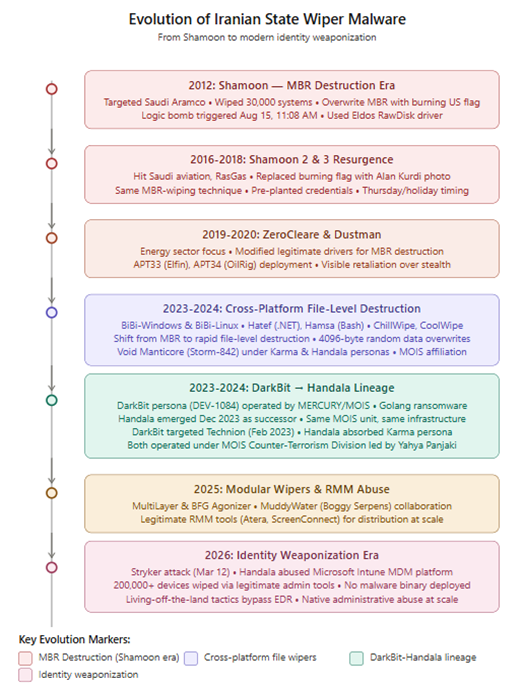
On February 28, 2026, the US and Israel launched coordinated military strikes against Iran (Operation Epic Fury / Roaring Lion). Iran’s Supreme Leader Khamenei was killed on March 01 and it hit back with drone and missile attacks across the Gulf, and the cyber dimension exploded almost immediately.
Iran’s domestic internet dropped to 1-4% within hours of the first strikes. That didn’t slow things down, dozens of threat groups operating outside Iran, plus pre-planted backdoors inside target networks, kept the attacks running at full speed.
The key shift this time around: Iran didn’t just rely on custom malware. The Stryker attack showed they’re now abusing legitimate IT tools with no malware. Meanwhile, China-aligned Mustang Panda quietly rode the news cycle to collect intelligence, and a wild-card criminal group (TeamPCP) deployed a Kubernetes wiper targeting Iranian infrastructure. It’s messy, multi-actor, and it’s still ongoing.
Iran’s Layered Cyber Operational Model
Iran’s cyber ecosystem operates through a layered structure that combines state-directed APT groups (IRGC-linked and MOIS-linked); semi-official contractors and front entities; hacktivist personas and collectives operated by intelligence services; and ideologically aligned foreign collectives operating in parallel. The Stryker Corporation attack on March 11, 2026 marked a significant escalation: a destructive wiper operation against the US, executed without malware by abusing legitimate MDM infrastructure representing a qualitative shift in Iranian operational capability and willingness to target Western corporate infrastructure.
Active Threats
Iran-State APT Groups
Seedworm / MuddyWater (MOIS)
Confirmed active on US and Israeli networks since at least early February before the strikes even started. Targets: bank, airport, NGO, and the Israeli arm of a US company. Two new backdoors were found:
- Dindoor: runs via Deno (JavaScript runtime). Signed with cert ‘Amy Cherne’. Found on the bank, software company, and Canadian NGO.
- Fakeset: Python-based. Pulled from Backblaze cloud storage. Signed with ‘Amy Cherne’ and ‘Donald Gay’ certs. The Donald Gay cert previously signed Stagecomp and Darkcomp, both confirmed Seedworm tools.
Rclone was used to try to exfiltrate data to a Wasabi S3 bucket from the compromised software company. MuddyWater also ran a parallel campaign (Operation Olalampo) across Middle East, Turkey, and Africa with overlapping infrastructure.
TA453 / APT42 / Charming Kitten (IRGC)
On March 8, despite Iran’s internet blackout, TA453 sent a credential phishing email to a US think tank. The actor posed as a policy researcher, built rapport over benign email, then sent a OneDrive-themed phishing page hosted on Netlify. Tracking pixels on a compromised site were used to see if the target clicked. The full domestic blackout didn’t stop them, overseas infrastructure kept them operational.
TA402 / OilRig / APT34 (MOIS)
Targeted a Middle Eastern government using a compromised Iraqi Ministry of Foreign Affairs email account. The lures referenced ‘Potential US ground operation in Iran’ and ‘Gulf military alliance.’ The payload either a decoy PDF or a credential harvesting page was served based on the target’s IP geolocation. Same compromised Iraqi MoFA infrastructure was also used by the Dust Specter cluster.
Marshtreader / Agrius / Pink Sandstorm (MOIS)
Expanded camera scanning post-strikes across Israel, UAE, Qatar, Bahrain, Kuwait, Lebanon, and Cyprus. Exploiting CVE-2017-7921 and CVE-2023-6895 on Hikvision cameras and video intercom units. This pattern compromises external cameras near conflict zones and is used to get real-time visual intel on strike damage. Any org with internet-facing cameras in these regions should treat this as an active threat.
Handala’s Stryker Corporation Attack
The most impactful Iran-attributed attack against a Western company in this conflict. On March 11, Handala (also tracked as Void Manticore, Storm-0842) wiped Stryker Corporation, a $25B medical device company with a $450M US supply contract.
How it worked
The attacker got hold of a compromised Microsoft 365 Global Admin account (likely from an old infostealer log sold on a criminal marketplace). With that account, researchers believe they logged into Microsoft Intune and used the legitimate ‘factory reset device’ feature to remotely wipe 200,000+ laptops, servers, and mobile devices across 79 countries. Login screens were replaced with the Handala logo.
- Stryker’s Cork, Ireland office (4,000–5,500 staff) was hit hardest with manufacturing systems disabled
- Order processing, manufacturing, and global shipping all disrupted (confirmed in SEC filing)
- SYK stock dropped on disclosure
- 50 TB of data allegedly exfiltrated beforehand (unverified in full)
- CISA deployed technical assistance; Ireland NCSC responded
Around March 20, the DOJ formally attributed Handala to Iran’s MOIS, calling it a ‘fake activist persona’ used for hack-and-leak and psychological operations. FBI Director Kash Patel announced the seizure of four Handala websites including its leak site. Check Point Research linked Handala’s leadership to the MOIS Counter-Terrorism Division, the same division whose reported head was killed in the March 2026 strikes.
On March 13, Handala also threatened a 40 TB wipe operation tied to Quds Day. No confirmed victim identified so far. They separately claimed a breach of Verifone; Verifone denied any attack.
Dust Specter (Iran-Nexus, Iraq Gov Targeting)
A previously unknown Iran-nexus APT targeting Iraqi government officials from January 2026 onward has been documented by researchers. The group compromised a legitimate Iraqi government website to host payloads and used a fake Cisco Webex for Government meeting as a ClickFix social engineering lure. Four new .NET malware tools found:
- SPLITDROP: dropper that extracts the next stage from a password-protected RAR and sideloads it via legitimate binaries like VLC or WingetUI
- TWINTASK: worker that executes PowerShell scripts by polling in.txt/out.txt files. Persists via HKCU Run key.
- TWINTALK: C2 module using HTTPS with randomized URIs, geofencing (checks victim’s location), and User-Agent spoofing mimicking Chrome.
- GHOSTFORM: later-stage RAT that combines TWINTASK and TWINTALK in a single binary with in-memory PowerShell. Uses a mutex to run only once and generates a bot ID from the assembly creation timestamp.
Unusual code artifacts in TWINTALK and GHOSTFORM like emojis, Unicode oddities, placeholder hex constants (0xABCDEF) suggest generative AI was used in parts of the development. This is the first confirmed AI-assisted malware coding observed in Iranian APT tooling at scale.
China APT – Mustang Panda (LOTUSLITE)
On March 4, researchers caught Mustang Panda (also tracked as Earth Preta, TA416, Bronze President) pivoting to Middle East conflict lures within days of the Feb 28 strikes. This is typical Mustang Panda behavior as they adapt lures to whatever is in the news.
The malicious ZIP contained a legitimate KuGou music binary renamed ‘Iran Strikes U.S. Military Facilities Across Gulf Region.exe’ and a malicious DLL (libmemobook.dll). When the exe runs, it sideloads the DLL which:
- Downloads WebFeatures.exe and kugou.dll from a compromised domain (e-kflower[.]com)
- Sets persistence via Run key (ACboardCm / ASEdge)
- dll is the LOTUSLITE backdoor — communicates to C2 172.81.60[.]97 via WinHTTP
LOTUSLITE has already been documented in January 2026 using Venezuela-themed lures with the exact same C2 IP. Same backdoor, same delivery chain but just different news hook. Attribution: moderate confidence to Mustang Panda based on KuGou binary abuse (documented tradecraft since 2022), shared C2, and embedded code messages denying Russian origin (previously seen in Mustang Panda’s ClaimLoader campaigns).
A separate GCC-targeted LNK/CHM campaign dropped a decoy PDF about ‘Iranian missile strikes on US base in Bahrain’ alongside a shellcode loader that uses RC4 key ‘20260301@@@’ to decrypt the next stage.
Hacktivist Groups – The Visible Layer
The hacktivist activity is noisy but mostly low-impact technically. DDoS, defacements, and hack-and-leak claims dominate. Many claims are exaggerated. However, a few groups have real capability and are worth tracking:
| Group | Confirmed/Claimed Operations | Links |
| Handala / Void Manticore | Stryker wiper (confirmed). Israeli healthcare. 1.3TB oil/gas claimed. Doxing of diaspora critics with death threats via email. | MOIS |
| FAD Team / Fatimiyoun | Wiper malware, SCADA/PLC access claims (Israel + allies). Turkish media attack. | IRGC-adjacent |
| Cyber Islamic Resistance (313 Team, RipperSec) | Drone defense system claimed. Israeli payment infra. Kuwait gov DDoS. | Pro-Iranian |
| DieNet | Bahrain airport, Sharjah airport, Riyadh Bank, Bank of Jordan — all DDoS. | Pro-Iranian |
| NoName057(16) | Israeli municipal, telecom, defense DDoS. Coordinated with Iranian groups. | Pro-Russian |
| Cardinal | Claimed IDF network access; leaked document referencing Operation Northern Shield. | Pro-Russian |
| Russian Legion | Claimed Iron Dome radar access (unverified). Claimed IDF server access. | Pro-Russian |
| Z-Pentest | Claimed US ICS/SCADA and CCTV compromise on Feb 28–Mar 2. | Pro-Russian |
Researchers tracked a detailed Telegram timeline of hacktivist activity from Feb 28 onwards. The Electronic Operations Room, an umbrella coordination channel, was stood up on the day of the strikes and served as a central hub for target sharing and claim coordination across 53+ groups.
MOIS Telegram C2 Malware
The FBI released a public FLASH (IC3, March 20) warning that MOIS cyber actors have been using Telegram bots as C2 infrastructure since Fall 2023, targeting Iranian dissidents, journalists, and opposition groups globally. The malware uses a two-stage design:
- Stage 1 masquerades as common apps: Telegram_authenticator.exe, KeePass.exe, WhatssApp.exe, Pictory_premium_ver9.0.4.exe. Drops Stage 2 on execution.
- Stage 2 persistent implant that connects to api.telegram[.]org for bidirectional C2. Related modules record screen and audio during Zoom sessions (MicDriver.zip).
The FBI also confirmed that Handala’s July 2025 hack-and-leak operation against dissidents used this same malware to harvest the leaked data. This bulletin formally ties Handala’s dissident-targeting activity to the broader MOIS Telegram C2 infrastructure.
Operation CamelClone
Seqrite Labs APT Team identified a multi-region espionage campaign using identical infection techniques across four countries: Algeria (Ministry of Housing lure), Mongolia (MonAtom LLC / nuclear energy lure), Ukraine (Algerian-Ukrainian cooperation lure), and Kuwait (Kuwait Air Force weapons requirements lure).
Every campaign follows the same chain: ZIP → LNK with PowerShell → downloads HOPPINGANT (f.js JavaScript loader) from filebulldogs[.]com → drops Rclone v1.70.3 (renamed l.exe) → XOR-decodes MEGA credentials (key: 56) → exfiltrates Desktop .doc/.docx/.pdf/.txt files and Telegram Desktop session data (tdata folder) to MEGA accounts registered via onionmail.org. Four separate MEGA accounts identified, all created Feb–March 2026.
Attribution: unknown. Targeting pattern (government, defense, diplomatic, energy across major-power rivalry flashpoints) suggests state-level intelligence collection.
TeamPCP – CanisterWorm / Kubernetes Wiper
A financially motivated cloud threat actor (TeamPCP, also tracked as DeadCatx3, PCPcat, ShellForce) added a geopolitically targeted wiper to their existing toolset. On March 19, they first executed a supply-chain attack against Trivy (Aqua Security’s popular vulnerability scanner), backdooring GitHub releases and Docker images to steal SSH keys, cloud credentials, K8s tokens, and crypto wallets from anyone running Trivy in CI/CD pipelines.
On March 22, they deployed a new payload via the same ICP canister C2 (tdtqy-oyaaa-aaaae-af2dq-cai[.]raw[.]icp0[.]io). This payload checks the system’s timezone and locale. If it matches Iran (Asia/Tehran, fa_IR):
- On Kubernetes: deploys a DaemonSet named ‘host-provisioner-iran’ across all nodes. Each pod runs an Alpine container named ‘kamikaze’ that deletes all top-level host directories and force-reboots the node.
- On non-Kubernetes Iranian hosts: runs rm -rf / –no-preserve-root
- On non-Iranian Kubernetes hosts: installs the CanisterWorm backdoor as a systemd service (pgmonitor) for ongoing credential theft
It’s unclear whether any Iranian systems were actually wiped, the malicious canister was only active for a short window and was swapped in and out rapidly. Researchers note the group seems partly attention-seeking. But the supply chain vector (Trivy runs in millions of dev environments), and the destructive geopolitically targeted payload are both real and notable. TeamPCP also hijacked Aqua Security’s private GitHub org on March 22, renaming all 44 internal repos to ‘tpcp-docs-*’ with description ‘TeamPCP Owns Aqua Security.’
IRGC Surveillance Expansion
Iran Wire reported that the IRGC issued a direct warning to Iranian citizens: Instagram and Telegram activity is being actively monitored. Iranian intelligence services have significantly expanded domestic surveillance operations since the strikes, cross-referencing social activity against known dissident profiles. This connects directly to the FBI FLASH’s Telegram C2 campaign, the same infrastructure used to attack dissidents abroad is being expanded domestically.
The Handala group’s use of Starlink during Iran’s internet blackout confirms that Iranian-linked threat actors have already planned around domestic connectivity suppression. A blanket internet shutdown no longer neutralizes these actors.
Sector Exposure
| Sector | Risk Level | Observed / Anticipated Targeting |
| Energy — Oil & Gas | CRITICAL | Handala 1.3TB exfil claimed from Gulf operators. SCADA/PLC access claims. Navigation disruption affecting 1,100+ ships near Strait of Hormuz. IRGC drone strikes on AWS Bahrain. Predatory Sparrow previously drained $90M from Iranian crypto exchange. |
| Government & Defense | CRITICAL | All Iranian APT groups. Dust Specter targeting Iraq MoFA. Kuwait/Jordan/Bahrain government sites DDoS. UNG0801 targeting Israeli government IT. CamelClone targeting Algeria, Mongolia, Kuwait, Ukraine defense/diplomatic bodies. |
| Financial Services | HIGH | Israeli banks DDoS. Riyadh Bank. Bank of Jordan. UAE vishing. Tarnished Scorpius Israeli target. Fake SSA portals and Kvish 6 toll payment phishing (Iran-aligned). |
| Healthcare | HIGH | Stryker Corporation wiper (200K+ devices wiped globally — DOD supplier). Handala breach of Israeli healthcare network (Clalit). CISA-level incident response deployed. |
| Defense Industry & Supply Chain | HIGH | Stryker Corporation ($450M DoD contract). U.S. supplier (Seedworm Dindoor). Supply chain compromise increasingly used to reach multiple high-value targets simultaneously. |
| Aviation & Transportation | HIGH | Bahrain airport DDoS. Sharjah/UAE airport DDoS. U.S. airport on Seedworm victim list. Strait of Hormuz shipping GPS spoofing affecting 1,100+ vessels. |
| Telecommunications | HIGH | Historical IRGC/MOIS priority sector. Infrastructure disruption and ISP targeting to locate dissidents. Sustained espionage campaigns. |
| Critical Infrastructure (OT/ICS) | HIGH | SCADA/PLC access claims by Cyber Islamic Resistance, FAD Team. Camera scanning by Marshtreader. Z-Pentest claimed U.S. ICS/SCADA and CCTV compromise (Feb 28–Mar 2). |
| IT / MSPs / Software | MEDIUM–HIGH | UNG0801 / Operation IconCat specifically targets Israeli IT, MSPs, HR, software. Seedworm compromised Israeli defense-sector software supplier. Supply chain entry point for downstream victims. |
| NGOs & Think Tanks | MEDIUM–HIGH | TA453/APT42 targeting U.S. think tank (credential phishing). Canadian NGO on Seedworm victim list. UNG0801 targets Israeli enterprise environments. |
| Media & Influence Ops | MEDIUM | FAD Team targeted Turkish media. Fake news blogs distributing StealC. Hacktivist psychological operations via Telegram and X. |
What to Watch For
- More Intune/MDM attacks against enterprises with large Microsoft-managed device fleets. Any org where a compromised Global Admin account can trigger mass device wipes is exposed the same way Stryker was.
- Handala has threatened a second wave tied to Quds Day. Monitor their Telegram channels and X feed for target announcements.
- Pre-positioned Seedworm access will likely get activated. The group was already inside US and Israeli networks before the war started, those footholds exist for a reason.
- More supply-chain attacks. TeamPCP’s Trivy compromise and Mustang Panda’s theme-jumping both show that attackers are comfortable using the developer toolchain and news cycle as attack vectors simultaneously.
- Wiper risk stays high. Druidfly, FAD Team, and Handala all have working wiper capability. BibiWiper, Hatef, and the Stryker MDM-wipe method represent three separate delivery approaches.
- MOIS Telegram C2 expansion. The FBI FLASH covers attacks going back to 2023. Expect the same malware (Pictory, KeePass, WhatsApp lookalikes) to be retargeted at diaspora, researchers, and journalists outside Iran.
- More China-aligned opportunistic collection using conflict themes not limited to Mustang Panda. Any major geopolitical development gets weaponized as a phishing lure within 48–72 hours.
What Your Team Should Do
Right now
- Check your Microsoft 365 Global Admin and Intune admin accounts. Do ALL of them have phishing-resistant MFA (FIDO2 or certificate-based)? If not, fix this first.
- Set an alert for any Intune action that wipes or factory-resets more than N devices. That threshold should be very small for a human-initiated action.
- If you use Trivy in CI/CD, check which version you’re pinned to. Versions 0.69.4–0.69.6 are compromised. Pin to a verified safe version by commit SHA, not by tag.
- Pull the MOIS Telegram C2 file hashes from Section 3.2 and run them through your EDR. These have been active since 2023.
- Check for Rclone, AnyDesk, ScreenConnect, and PDQConnect running in places you didn’t install them. CamelClone, Seedworm, and Handala all abuse legitimate tools.
This week
- Run an authentication review. Look for logins from unusual countries, off-hours access, and any new admin accounts created in the last 60 days.
- Check outbound traffic for unexpected connections to MEGA, Backblaze, Wasabi, and Telegram API (api.telegram[.]org) from server processes not browser traffic.
- Test your backup restoration. Specifically: can you rebuild a critical server from an air-gapped backup if your primary environment is wiped? If the answer takes more than an hour to verify, that’s the gap.
- If you have Kubernetes deployments: audit your DaemonSets in kube-system. Look for ‘host-provisioner-*’ or ‘provisioner’ containers. Check for Alpine containers with hostPath: / mounts.
- Brief your team on conflict-themed phishing. The lure themes in active use: Iranian missile strikes, JCPOA updates, Gulf military alliance, civil defense alerts, Kuwait Air Force procurement, cooperation proposals.
Ongoing
- Monitor Telegram and X for target lists and breach claims tied to your org or sector. Hacktivist groups post their next targets before they attack.
- Subscribe to CISA’s Iran advisory feed and UK NCSC alerts for this conflict.
- Review your CI/CD pipeline permissions. Service accounts with PATs (Personal Access Tokens) and no MFA are exactly what TeamPCP used to own Aqua Security’s GitHub org.
- Talk to your cyber insurance provider about war exclusion clauses. The Stryker attack has confirmed state attribution (DOJ). Policies may not cover state-directed destruction.
References
- https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- https://unit42.paloaltonetworks.com/evolution-of-iran-cyber-threats/
- https://www.ic3.gov/CSA/2026/260320.pdf
- https://www.security.com/threat-intelligence/iran-cyber-threat-activity-us
- https://www.rapid7.com/blog/post/tr-iran-cyber-playbook-escalating-regional-conflict/
- https://www.zscaler.com/blogs/security-research/middle-east-conflict-fuels-opportunistic-cyber-attacks
- https://www.zscaler.com/blogs/security-research/dust-specter-apt-targets-government-officials-iraq
- https://www.acronis.com/en/tru/posts/lotuslite-targeted-espionage-leveraging-geopolitical-themes/
- https://www.seqrite.com/blog/operation-camelclone-multi-region-espionage-campaign-targets-government-and-defense-entities-amidst-regional-tensions/
- https://www.seqrite.com/blog/ung0801-tracking-threat-clusters-obsessed-with-av-icon-spoofing-targeting-israel/
- https://www.bleepingcomputer.com/news/security/teampcp-deploys-iran-targeted-wiper-in-kubernetes-attacks/
- https://www.bleepingcomputer.com/news/security/trivy-supply-chain-attack-spreads-to-docker-github-repos/
- https://www.aikido.dev/blog/teampcp-stage-payload-canisterworm-iran
- https://krebsonsecurity.com/2026/03/canisterworm-springs-wiper-attack-targeting-iran/
- https://www.reuters.com/technology/iran-linked-hackers-restore-website-after-us-seizes-domains-2026-03-20/
- https://iranwire.com/en/news/150668-irgc-warns-citizens-your-instagram-and-telegram-activity-is-being-watched/
- https://socradar.io/blog/telegram-activity-timeline-iran-israel-us-war/
- https://www.proofpoint.com/us/blog/threat-insight/iran-conflict-drives-heightened-espionage-activity
- https://www.intel471.com/blog/israeli-us-strikes-against-iran-triggers-a-surge-in-hacktivist-activity
- https://techcrunch.com/2026/03/20/u-s-accuses-irans-government-of-operating-hacktivist-group-that-hacked-stryker/
- https://www.sophos.com/en-us/blog/hacktivist-campaigns-increase-as-united-states-iran-and-israel-conflict
- https://research.checkpoint.com/2026/handala-hack-unveiling-groups-modus-operandi/
- https://www.cloudsek.com/blog/middle-east-escalation-israel-iran-us-cyber-war-2026
- https://www.ncsc.gov.uk/news/ncsc-advises-uk-organisations-take-action-following-conflict-in-middle-east
- https://www.cisa.gov/topics/cyber-threats-and-advisories/advanced-persistent-threats/iran
Authors:
Shayak Tarafdar
Deepak Thomas Philip
Sathwik Ram Prakki
Kartikkumar Jivani

