Quick Heal Threat Reports are collated after intensive research by our Threat Research and Response Team. They provide an overview and analysis of threat activity reported from Quick Heal installations all over the world.
The recently launched Quick Heal Annual Threat Report 2017 presents a detailed insight into the state of digital security for Windows and Android users. It includes malware detection statistics, top threats, important trends, and security predictions. Here are some excerpts from the report.
1. TrojanDropper.Dexel.A5 is a malicious Windows malware that enters user systems via email attachments and malicious websites. The malware steals confidential data from infected systems and can destroy user data permanently.
2. Propagated through third-party app stores, Android.Triada.F Trojan hides its icon and silently runs in the background downloading and installing several other malicious apps.

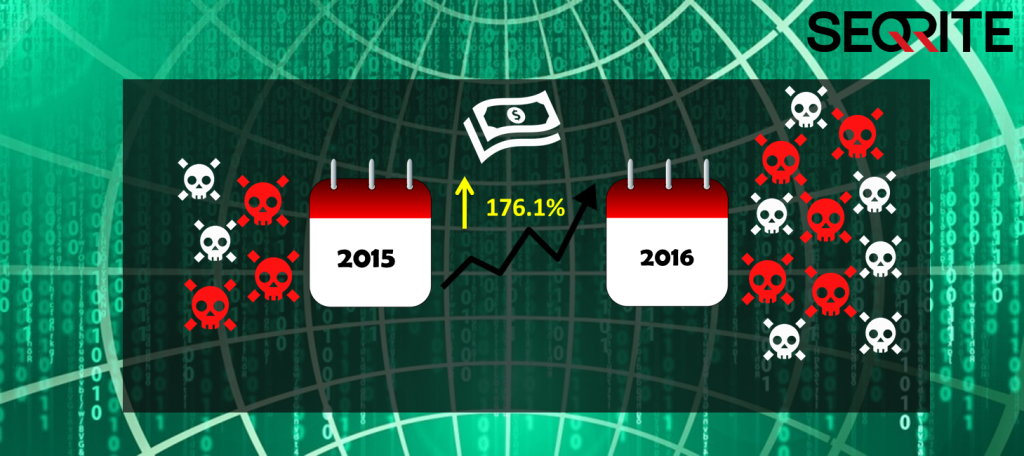
3. In its Annual Threat Report, Quick Heal Labs reported a 176.1% rise in banking malware threats when compared with 2015.
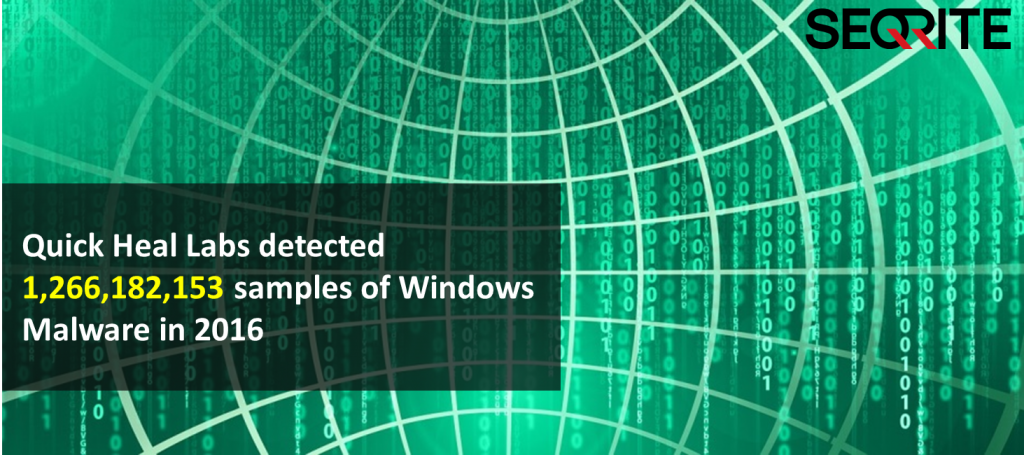
4. Quick Heal Labs detected over 1.2 billion malware affecting the Windows platform in 2016, with Q1 clocking the highest detection rate.
To get a detailed report on these insights and more, download Quick Heal Annual Threat Report 2017.




