From Encryption to Real-World Attack Prevention
In today’s hyper-connected digital environment, secure communication is not just about encrypting data—it is about preventing attackers from abusing exposed services. Secure communication protocols protect data in transit, but misconfigurations and weak access controls often turn legitimate protocols into attack vectors.
This blog explores secure communication protocols, their implementation, real-world threats such as brute-force attacks, and practical defensive measures aligned with industry best practices.
1. Introduction to Secure Communication Protocols
Secure communication protocols are standardized rules and mechanisms that protect data exchanged across networks. Their primary goals are:
- Confidentiality – preventing unauthorized disclosure
- Integrity – ensuring data is not altered in transit
- Authentication – verifying the identity of communicating parties
Without these protocols, attackers can intercept, manipulate, or impersonate legitimate communications.
2. Core Secure Communication Protocols
TLS/SSL
TLS (formerly SSL) is the backbone of secure internet communication.
- Use cases: HTTPS, APIs, email transport
- Security model: Asymmetric key exchange + symmetric encryption
- Implementation: Requires valid certificates issued by trusted Certificate Authorities (CAs)
IPsec
IPsec secures communication at the network layer.
- Use cases: VPNs, site-to-site tunnels
- Modes: Transport (payload only), Tunnel (entire packet)
- Strength: Protects traffic regardless of application
SSH
SSH enables secure remote administration.
- Use cases: Remote login, command execution, file transfer
- Security: Public key authentication and encrypted sessions
S/MIME
S/MIME secures email communication using PKI.
- Capabilities: Email encryption and digital signatures
- Trust model: Certificate-based identity verification
HTTPS
HTTPS combines HTTP with TLS to secure web traffic.
- Critical for: E-commerce, authentication portals, APIs
- Risk if misconfigured: Weak ciphers or expired certificates.
3. Where Secure Protocols Fail in Practice
Even when secure protocols are deployed, attackers often bypass encryption by targeting authentication weaknesses, especially on services exposed to the internet.
Commonly abused services:
- SMB (445)
- RDP (3389)
- MSSQL (1433)
The most frequent attack technique against these services is the brute-force attack, where automated tools attempt thousands of credential combinations until access is gained.
4. Brute-Force Attacks: Turning Secure Services into Entry Points
What Is a Brute-Force Attack?
A brute-force attack systematically attempts multiple username and password combinations to gain unauthorized access. Once successful, attackers may:
- Deploy malware or ransomware
- Steal sensitive data
- Establish persistent access
These attacks are especially effective against publicly exposed services with weak authentication controls.
5. Attack Flow (Conceptual Diagram)
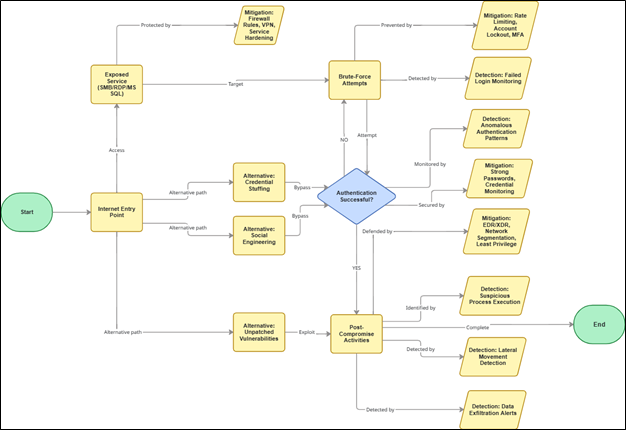
This flow highlights a critical reality: encryption alone does not stop credential abuse.
6. MITRE ATT&CK Mapping
| Attack Stage | MITRE Technique |
| Credential Guessing | T1110 – Brute Force |
| Valid Account Abuse | T1078 – Valid Accounts |
| Remote Access | T1021 – Remote Services |
| Credential Access (Post-Compromise) | T1003 – OS Credential Dumping |
| Persistence | T1053 – Scheduled Tasks / Jobs |
This mapping shows how a simple brute-force attempt can evolve into a full intrusion lifecycle.
7. Defensive Controls: Securing Services Beyond Encryption
Authentication Hardening
- Use strong, unique, complex passwords
- Avoid default usernames such as Administrator, Admin, SA, root
- Enforce periodic password rotation policies
Account Lockout Policies
- Lock accounts after a defined number of failed attempts
- Apply time-based or administrator-unlock policies to slow automated attacks
MSSQL-Specific Protection
- Disable default SA account
- Change default port 1433
- Restrict public access to database services
- Apply least-privilege access controls
Network Exposure Reduction
- Monitor and restrict access to common attack ports:
- SMB – 445
- RDP – 3389
- MSSQL – 1433
- Allow access only from trusted IP addresses
VPN Over Direct Exposure
Use VPNs with encrypted tunnels instead of direct NAT or port forwarding to reduce attack surface.
Multi-Factor Authentication (MFA)
Enable MFA on all internet-facing services to render brute-force attacks ineffective, even if credentials are compromised.
Defensive Checklist
Use this as a quick security baseline:
- ☐ TLS/SSL certificates valid and using strong ciphers
- ☐ SMB, RDP, MSSQL not publicly exposed
- ☐ Strong password & lockout policies enforced
- ☐ Default accounts disabled or renamed
- ☐ MFA enabled on external services
- ☐ VPN used instead of direct access
- ☐ IDS/IPS logs reviewed regularly
- ☐ Common ports strictly monitored
- ☐ Incident response plan documented
8. Conclusion
Secure communication protocols are foundational to cybersecurity—but they are not sufficient on their own. Real-world security requires combining encryption with strong authentication, controlled exposure, continuous monitoring, and incident readiness.
By aligning secure protocol implementation with brute-force prevention strategies and MITRE ATT&CK–informed defenses, organizations can significantly reduce their attack surface and strengthen their overall security posture.
Authors:




